
Get the free Detecting Vulnerabilities of
Show details
Detecting Vulnerabilities of
Broadcast Receivers in Android
Applications
BDI Diana Thesis Submitted in Partial Fulfillment
of the Requirements for the Degree of Master of Science (M.Sc.)computer ScienceFaculty
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign detecting vulnerabilities of
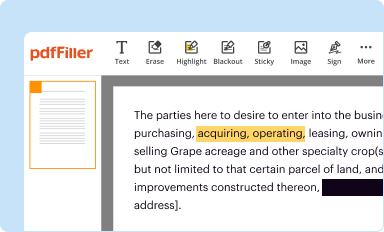
Edit your detecting vulnerabilities of form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
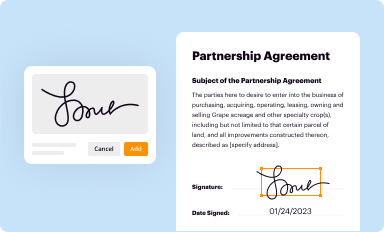
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
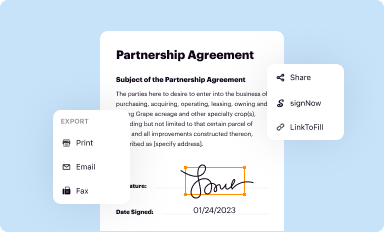
Share your form instantly
Email, fax, or share your detecting vulnerabilities of form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit detecting vulnerabilities of online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in to account. Click Start Free Trial and register a profile if you don't have one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
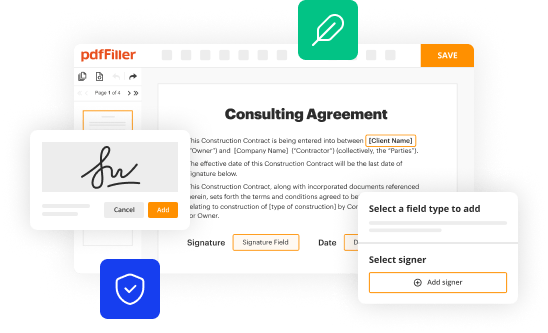
Edit detecting vulnerabilities of. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out detecting vulnerabilities of
How to fill out detecting vulnerabilities of
01
To fill out detecting vulnerabilities of, follow these steps:
02
Start by conducting a thorough assessment of the system or application in question.
03
Identify potential entry points or weak areas that could be exploited by attackers.
04
Use automated vulnerability scanning tools to scan the system or application for known vulnerabilities.
05
Perform manual testing and analysis to identify any additional vulnerabilities that may not be detectable by automated tools.
06
Prioritize the vulnerabilities based on their severity and potential impact on the system or application.
07
Develop a plan to remediate or mitigate the identified vulnerabilities.
08
Implement necessary security measures, such as patches, updates, or configuration changes, to address the vulnerabilities.
09
Regularly reassess the system or application to detect any new vulnerabilities that may have emerged.
10
Keep up to date with the latest security best practices and stay informed about new vulnerabilities and attack vectors.
Who needs detecting vulnerabilities of?
01
Detecting vulnerabilities is crucial for anyone who has a system or application that is connected to a network or the Internet.
02
This includes individuals, businesses, organizations, and governments.
03
By detecting vulnerabilities, these entities can proactively protect their systems and data from potential breaches or attacks.
04
It is especially important for those who handle sensitive or confidential information, such as personal data, financial records, or trade secrets.
05
Ultimately, anyone who wants to maintain the security and integrity of their systems and protect against potential threats can benefit from detecting vulnerabilities.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my detecting vulnerabilities of in Gmail?
You may use pdfFiller's Gmail add-on to change, fill out, and eSign your detecting vulnerabilities of as well as other documents directly in your inbox by using the pdfFiller add-on for Gmail. pdfFiller for Gmail may be found on the Google Workspace Marketplace. Use the time you would have spent dealing with your papers and eSignatures for more vital tasks instead.
How can I edit detecting vulnerabilities of on a smartphone?
The easiest way to edit documents on a mobile device is using pdfFiller’s mobile-native apps for iOS and Android. You can download those from the Apple Store and Google Play, respectively. You can learn more about the apps here. Install and log in to the application to start editing detecting vulnerabilities of.
Can I edit detecting vulnerabilities of on an iOS device?
Yes, you can. With the pdfFiller mobile app, you can instantly edit, share, and sign detecting vulnerabilities of on your iOS device. Get it at the Apple Store and install it in seconds. The application is free, but you will have to create an account to purchase a subscription or activate a free trial.
Fill out your detecting vulnerabilities of online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Detecting Vulnerabilities Of is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















