
Get the free managing cybersecurity risk - Lexpert
Show details
REGISTER ONLINE: www.lexpert.ca/legalprogramsGUEST SPEAKERSFULLY ACCREDITED INCL ASS PROGRAM & LIVE Webinars! Please register the following delegate(s) for MANAGING CYBERSECURITY RISK Name: Title:
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign managing cybersecurity risk
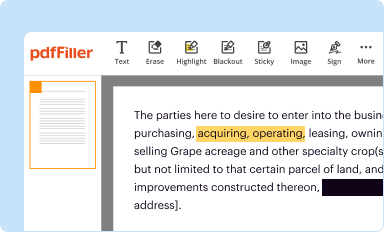
Edit your managing cybersecurity risk form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
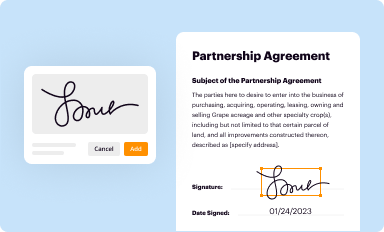
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
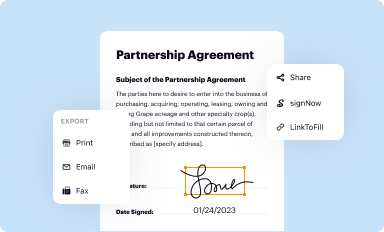
Share your form instantly
Email, fax, or share your managing cybersecurity risk form via URL. You can also download, print, or export forms to your preferred cloud storage service.
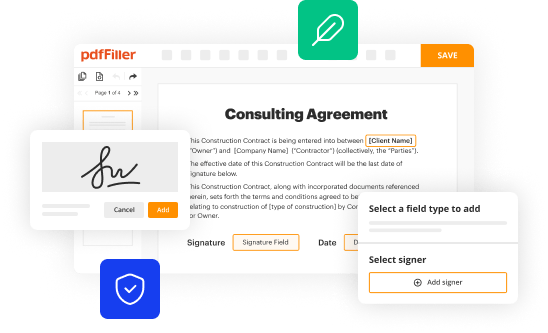
Editing managing cybersecurity risk online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Log in to account. Click Start Free Trial and sign up a profile if you don't have one.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit managing cybersecurity risk. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
With pdfFiller, it's always easy to work with documents.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out managing cybersecurity risk
How to fill out managing cybersecurity risk
01
To fill out managing cybersecurity risk, follow these steps:
02
Identify and prioritize assets: Start by identifying the critical assets that need protection and prioritize them based on their importance to the organization.
03
Conduct a risk assessment: Evaluate the potential vulnerabilities and threats that could compromise the security of the identified assets. This can be done through a combination of internal and external assessments.
04
Develop risk mitigation strategies: Once the risks are identified, develop strategies to mitigate them. This may involve implementing security controls, creating incident response plans, and conducting employee training on cybersecurity best practices.
05
Monitor and update: Regularly monitor the effectiveness of the implemented security measures and update them as necessary. Cyber threats evolve constantly, so it is crucial to stay updated with the latest trends and technologies.
06
Continuously review and improve: Managing cybersecurity risk is an ongoing process. Regularly review and improve the risk management strategy based on new threats, organizational changes, and lessons learned from past incidents.
07
Engage stakeholders: Involve all relevant stakeholders, including senior management, IT department, employees, and third-party vendors, in the risk management process. Collaboration and communication are key in ensuring a comprehensive and effective approach to managing cybersecurity risk.
Who needs managing cybersecurity risk?
01
Managing cybersecurity risk is crucial for any organization that stores and processes sensitive or confidential information, relies on technology infrastructure for its operations, or faces potential threats from cybercriminals.
02
This includes but is not limited to:
03
- Businesses of all sizes and industries
04
- Government agencies and departments
05
- Non-profit organizations
06
- Healthcare institutions
07
- Financial institutions
08
- Educational institutions
09
- Critical infrastructure providers
10
In today's digital age, virtually any organization that uses computers, networks, and the internet is susceptible to cyber threats. Therefore, managing cybersecurity risk is a necessity to protect the organization's reputation, customer data, and financial stability.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find managing cybersecurity risk?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific managing cybersecurity risk and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
Can I create an eSignature for the managing cybersecurity risk in Gmail?
With pdfFiller's add-on, you may upload, type, or draw a signature in Gmail. You can eSign your managing cybersecurity risk and other papers directly in your mailbox with pdfFiller. To preserve signed papers and your personal signatures, create an account.
How do I edit managing cybersecurity risk on an Android device?
With the pdfFiller Android app, you can edit, sign, and share managing cybersecurity risk on your mobile device from any place. All you need is an internet connection to do this. Keep your documents in order from anywhere with the help of the app!
What is managing cybersecurity risk?
Managing cybersecurity risk involves identifying, assessing, and mitigating potential threats to an organization's digital assets and systems to protect against cyber attacks and data breaches.
Who is required to file managing cybersecurity risk?
Certain organizations in specific industries, such as financial institutions and healthcare providers, may be required to file managing cybersecurity risk reports to regulatory bodies or government agencies.
How to fill out managing cybersecurity risk?
To fill out managing cybersecurity risk, organizations typically follow established cybersecurity frameworks and guidelines, conduct risk assessments, and implement security measures to address potential vulnerabilities.
What is the purpose of managing cybersecurity risk?
The purpose of managing cybersecurity risk is to safeguard sensitive data, protect critical systems, and prevent unauthorized access or malicious activities that could compromise an organization's operations or reputation.
What information must be reported on managing cybersecurity risk?
Organizations may be required to report on their cybersecurity policies, risk assessments, security controls, incident response procedures, and any breaches or security incidents that occurred during the reporting period.
Fill out your managing cybersecurity risk online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Managing Cybersecurity Risk is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















