Get the free Computer Forensics:
Show details
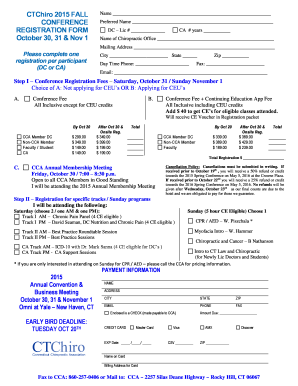
Computer Forensics: Investigation Procedures and Response, Second Edition Chapter 5 Incident HandlingObjectives After completing this chapter, you should be able to: Identify incidents Understand
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign computer forensics

Edit your computer forensics form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your computer forensics form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing computer forensics online
Use the instructions below to start using our professional PDF editor:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit computer forensics. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
With pdfFiller, it's always easy to deal with documents. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out computer forensics

How to fill out computer forensics
01
Start by ensuring that you have the necessary tools and software for computer forensics, such as a forensic imaging tool and a forensic analysis tool.
02
Make sure to work in a controlled and secure environment to prevent any contamination or tampering of digital evidence.
03
Begin the process by creating a forensically sound image of the target computer's storage media, such as the hard drive. This involves using a write-blocking device to prevent any modifications to the original data.
04
Once you have obtained the image, create a forensic backup copy and store it in a secure location.
05
Use the forensic analysis tool to analyze the image and retrieve relevant data or evidence. This may include searching for deleted files, analyzing internet browsing history, or examining system logs.
06
Document and record all the steps and procedures you perform during the computer forensics process.
07
Prepare a detailed report summarizing your findings, including any evidence collected and the methodology used.
08
It is important to maintain the integrity and confidentiality of the collected evidence at all times to ensure its admissibility in court, if required.
Who needs computer forensics?
01
Computer forensics is needed by various individuals and organizations, including:
02
- Law enforcement agencies and government agencies involved in criminal investigations.
03
- Private investigators hired to gather digital evidence for legal cases.
04
- Corporations and businesses concerned about internal fraud, data breaches, or intellectual property theft.
05
- Network security teams working to identify and analyze cyber attacks or intrusions.
06
- Legal professionals involved in litigation or civil disputes requiring electronic evidence.
07
- Individuals who suspect unauthorized access or hacking incidents on their personal computers or devices.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify computer forensics without leaving Google Drive?
pdfFiller and Google Docs can be used together to make your documents easier to work with and to make fillable forms right in your Google Drive. The integration will let you make, change, and sign documents, like computer forensics, without leaving Google Drive. Add pdfFiller's features to Google Drive, and you'll be able to do more with your paperwork on any internet-connected device.
Can I create an electronic signature for the computer forensics in Chrome?
Yes. By adding the solution to your Chrome browser, you may use pdfFiller to eSign documents while also enjoying all of the PDF editor's capabilities in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a photo of your handwritten signature using the extension. Whatever option you select, you'll be able to eSign your computer forensics in seconds.
How do I complete computer forensics on an Android device?
Use the pdfFiller mobile app to complete your computer forensics on an Android device. The application makes it possible to perform all needed document management manipulations, like adding, editing, and removing text, signing, annotating, and more. All you need is your smartphone and an internet connection.
What is computer forensics?
Computer forensics is the application of investigation and analysis techniques to gather and preserve evidence from a digital device in a way that is suitable for presentation in a court of law.
Who is required to file computer forensics?
Computer forensics is typically required to be filed by individuals or organizations involved in legal cases or investigations where digital evidence is involved.
How to fill out computer forensics?
Computer forensics is filled out by trained professionals who specialize in collecting and analyzing digital evidence using specialized tools and techniques.
What is the purpose of computer forensics?
The purpose of computer forensics is to uncover and preserve evidence stored on digital devices that can be used to investigate and prosecute crimes, misconduct, or security incidents.
What information must be reported on computer forensics?
Computer forensics reports typically include details of the methods used, evidence collected, analysis performed, and conclusions reached during the investigation.
Fill out your computer forensics online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Computer Forensics is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.