Get the free PHP Security best practices for Linux sys administrators:Top ... - docshare02 docshare
Show details
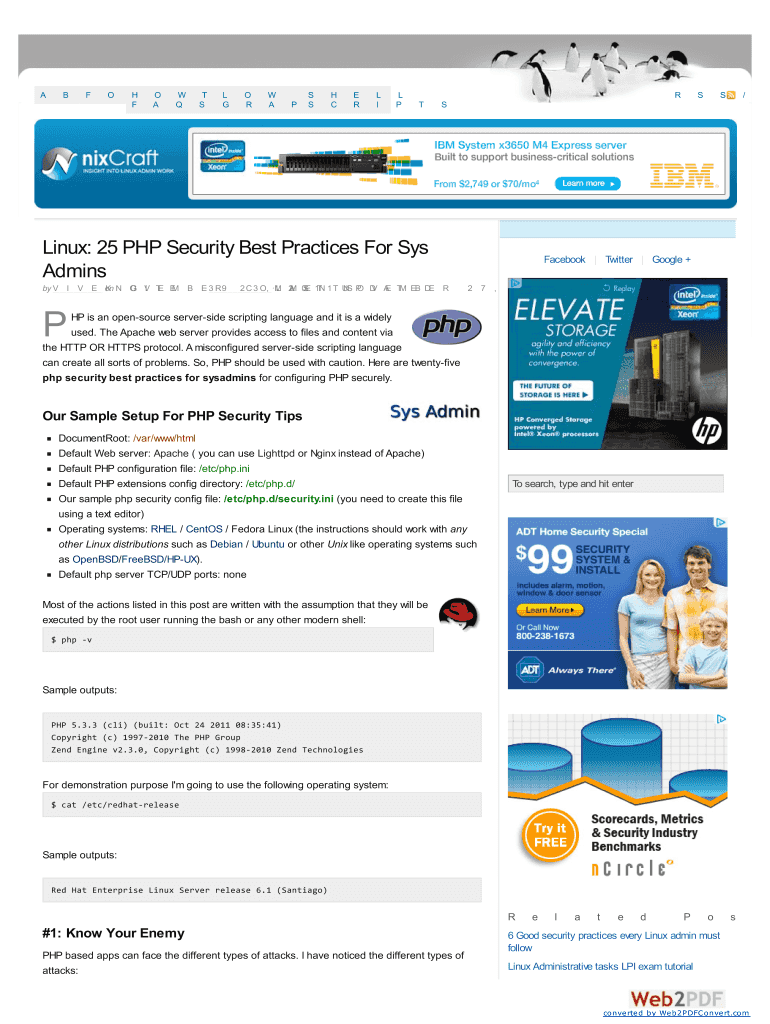
AGO FO UR T H FM O AM W QT SLO GO RAW A PS SHH CIE RTL ISL PR Linux: 25 PHP Security Best Practices For Says Admins by V I V E on K N O G V I TE EM B E 3 R 9SS/FS2 C 3 O, M L 2A M 0SE 1 TN 1 T US
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign php security best practices

Edit your php security best practices form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your php security best practices form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing php security best practices online
To use the professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit php security best practices. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out php security best practices

How to fill out php security best practices
01
To fill out PHP security best practices, follow these steps:
02
Use the latest version of PHP: Always use the latest stable version of PHP, as it includes security patches and fixes for vulnerabilities found in previous versions.
03
Validate and filter user input: Thoroughly validate and filter all user input to prevent SQL injection, cross-site scripting (XSS), and other attacks.
04
Use parameterized queries or prepared statements: When interacting with databases, use parameterized queries or prepared statements to avoid SQL injection.
05
Sanitize output data: Before displaying user-generated content, sanitize the data to prevent XSS attacks. Use functions like htmlentities() or htmlspecialchars().
06
Implement proper error handling: Error messages can expose sensitive information. Implement proper error handling to hide detailed error messages from attackers.
07
Validate and sanitize file uploads: Validate file types, restrict file sizes, and store uploaded files in a secure directory with limited permissions.
08
Implement secure authentication and password handling: Use secure password hashing algorithms (e.g., bcrypt) and enforce strong password policies like minimum lengths and complexity requirements.
09
Protect against CSRF attacks: Implement measures like CSRF tokens to protect against Cross-Site Request Forgery attacks.
10
Use secure session management: Store session data securely and regenerate session IDs after a user logs in or performs a significant action.
11
Keep up with security updates: Regularly update PHP, frameworks, libraries, and plugins to benefit from security patches and fixes.
12
Remember that PHP security best practices are an ongoing effort, and it is important to stay updated with the latest security techniques and practices.
Who needs php security best practices?
01
Anyone who develops or maintains PHP web applications should prioritize PHP security best practices. This includes individual developers, development teams, and organizations that use PHP for their web development.
02
Web applications built with PHP are vulnerable to various security threats, such as SQL injections, XSS attacks, session hijacking, and more. By implementing security best practices, developers can protect their applications, prevent data breaches, and ensure the integrity and confidentiality of user data.
03
Following PHP security best practices is particularly crucial for applications handling sensitive information, such as e-commerce websites, payment gateways, healthcare systems, and any other application involving personal or financial data.
04
Additionally, adhering to PHP security best practices is essential for compliance with industry standards and regulations, such as the General Data Protection Regulation (GDPR) or Payment Card Industry Data Security Standard (PCI DSS).
05
In summary, anyone involved in PHP web development, especially those handling sensitive information or aiming for compliance, should prioritize PHP security best practices.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my php security best practices in Gmail?
You can use pdfFiller’s add-on for Gmail in order to modify, fill out, and eSign your php security best practices along with other documents right in your inbox. Find pdfFiller for Gmail in Google Workspace Marketplace. Use time you spend on handling your documents and eSignatures for more important things.
Can I edit php security best practices on an iOS device?
No, you can't. With the pdfFiller app for iOS, you can edit, share, and sign php security best practices right away. At the Apple Store, you can buy and install it in a matter of seconds. The app is free, but you will need to set up an account if you want to buy a subscription or start a free trial.
How do I edit php security best practices on an Android device?
You can. With the pdfFiller Android app, you can edit, sign, and distribute php security best practices from anywhere with an internet connection. Take use of the app's mobile capabilities.
What is php security best practices?
PHP security best practices are guidelines and measures that developers can follow to secure their PHP applications from potential vulnerabilities and attacks.
Who is required to file php security best practices?
Developers and organizations that use PHP for their web applications are required to implement PHP security best practices.
How to fill out php security best practices?
PHP security best practices can be implemented by following industry standards, utilizing secure coding practices, updating software regularly, and conducting regular security audits.
What is the purpose of php security best practices?
The purpose of PHP security best practices is to protect PHP applications and sensitive data from unauthorized access, data breaches, and other security threats.
What information must be reported on php security best practices?
Information such as security measures implemented, vulnerabilities identified and patched, security protocols used, and any security incidents that occurred must be reported on PHP security best practices.
Fill out your php security best practices online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Php Security Best Practices is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.