Get the free Adventures in Cybersecurity: How to Respond When Workers ...
Show details
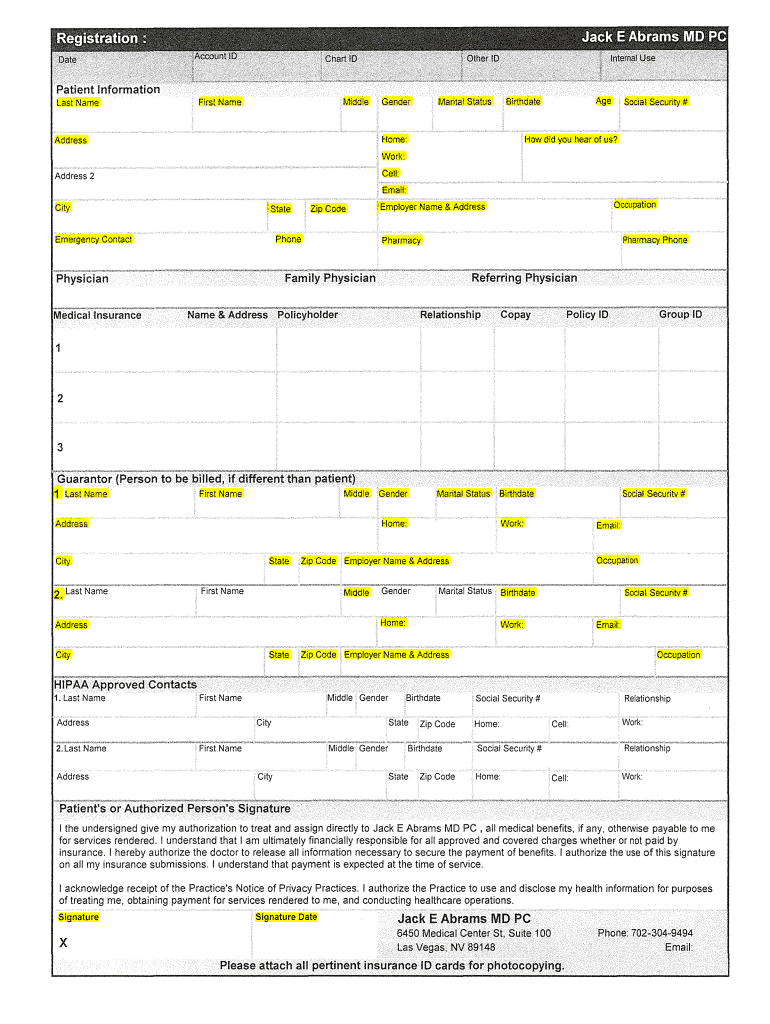
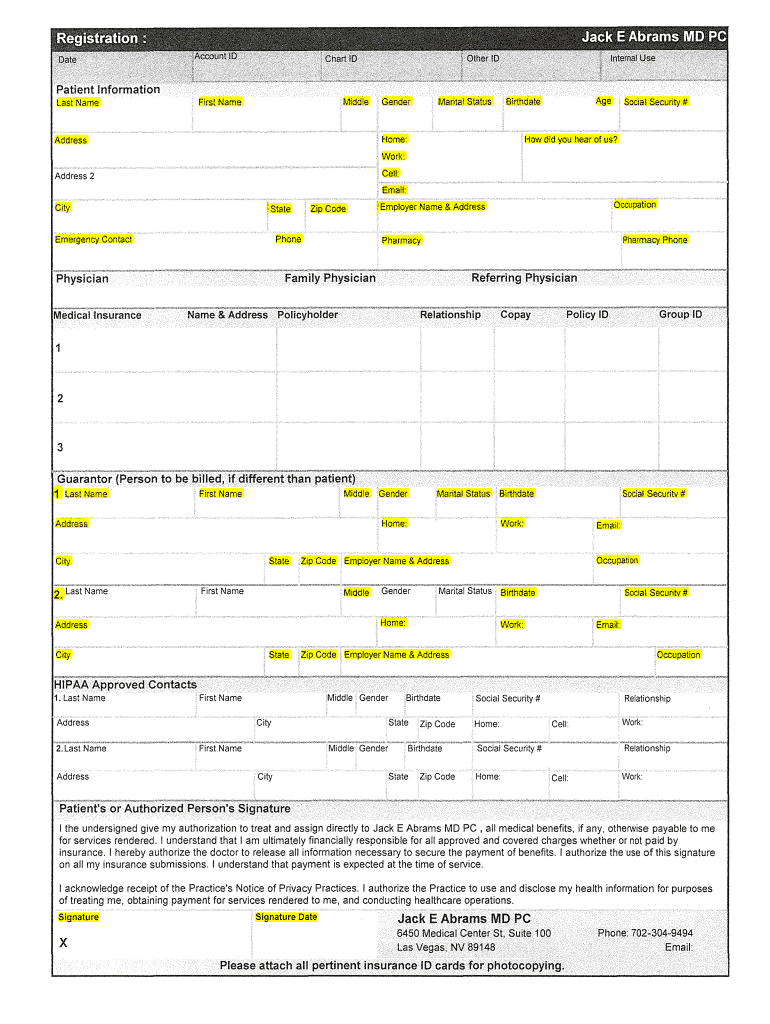
Patient Information Last NameMiddleFirst NameGenderMarital StatusBirthdateHome:AddressAgeSocial Security#How did you hear of us? Work: Cell:Address 2Email: CitystateZip CodePhoneEmergency ContactOccupation
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign adventures in cybersecurity how

Edit your adventures in cybersecurity how form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your adventures in cybersecurity how form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit adventures in cybersecurity how online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit adventures in cybersecurity how. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out adventures in cybersecurity how

How to fill out adventures in cybersecurity how
01
Begin by researching and gaining a thorough understanding of the different aspects of cybersecurity. This includes knowledge about different types of threats, vulnerabilities, attack vectors, and defense mechanisms.
02
Identify the specific area or subfield of cybersecurity you want to focus on, such as network security, data privacy, or ethical hacking.
03
Enroll in formal education programs or online courses to acquire the necessary knowledge and skills required for adventures in cybersecurity. These programs can include coursework in computer science, programming, cryptography, and information security.
04
Practice hands-on learning by participating in Capture the Flag (CTF) competitions, security hackathons, or bug bounty programs. These activities allow you to apply your skills in real-world scenarios and learn from experienced professionals.
05
Stay updated with the latest trends, technologies, and challenges in cybersecurity by regularly reading industry articles, attending conferences, and following cybersecurity experts on social media.
06
Engage in networking opportunities within the cybersecurity community to establish professional connections and learn from industry veterans.
07
Continuously improve your skills and knowledge through continuous learning and professional development. This can include pursuing advanced certifications like Certified Ethical Hacker (CEH) or Certified Information Systems Security Professional (CISSP).
08
Develop a strong ethical foundation and adhere to legal and ethical standards when conducting adventures in cybersecurity. Always prioritize the protection of individuals' privacy and the security of systems and data.
09
Finally, gain hands-on experience through internships, part-time jobs, or volunteer opportunities in cybersecurity firms or organizations. Practical experience will enhance your expertise and make you more desirable to potential employers.
Who needs adventures in cybersecurity how?
01
Adventures in cybersecurity how are needed by:
02
- Individuals aspiring to become cybersecurity professionals and want to gain practical experience and knowledge in the field.
03
- IT professionals who want to expand their career opportunities and specialize in the cybersecurity domain.
04
- Organizations and businesses that want to enhance their security posture and protect their sensitive information from cyber threats.
05
- Government agencies and intelligence organizations that need skilled cybersecurity professionals to defend against nation-state attacks and protect critical infrastructure.
06
- Ethical hackers and researchers who want to contribute to the cybersecurity community by identifying vulnerabilities and improving security practices.
07
- Individuals or businesses who have been victims of cyber attacks and want to learn how to better protect themselves from future threats.
08
- Anyone interested in understanding the complex world of cybersecurity and its importance in today's digital age.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send adventures in cybersecurity how for eSignature?
When you're ready to share your adventures in cybersecurity how, you can send it to other people and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail. You can also notarize your PDF on the web. You don't have to leave your account to do this.
Can I create an electronic signature for signing my adventures in cybersecurity how in Gmail?
Upload, type, or draw a signature in Gmail with the help of pdfFiller’s add-on. pdfFiller enables you to eSign your adventures in cybersecurity how and other documents right in your inbox. Register your account in order to save signed documents and your personal signatures.
How do I fill out the adventures in cybersecurity how form on my smartphone?
The pdfFiller mobile app makes it simple to design and fill out legal paperwork. Complete and sign adventures in cybersecurity how and other papers using the app. Visit pdfFiller's website to learn more about the PDF editor's features.
What is adventures in cybersecurity how?
Adventures in cybersecurity involve engaging in activities or experiences related to cybersecurity, such as ethical hacking, penetration testing, and incident response.
Who is required to file adventures in cybersecurity how?
Anyone involved in cybersecurity activities, including cybersecurity professionals, IT staff, and employees of organizations.
How to fill out adventures in cybersecurity how?
To fill out adventures in cybersecurity, individuals can document their experiences, skills, and knowledge in cybersecurity through a resume or portfolio.
What is the purpose of adventures in cybersecurity how?
The purpose of adventures in cybersecurity is to showcase individuals' expertise and capabilities in cybersecurity, and to demonstrate their commitment to continuous learning and development.
What information must be reported on adventures in cybersecurity how?
Information such as the types of cybersecurity activities engaged in, the duration of the activities, any certifications or training completed, and the impact of the activities on cybersecurity practices.
Fill out your adventures in cybersecurity how online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Adventures In Cybersecurity How is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















