Get the free Content analysis of cyber insurance policies: how do carriers ...
Show details
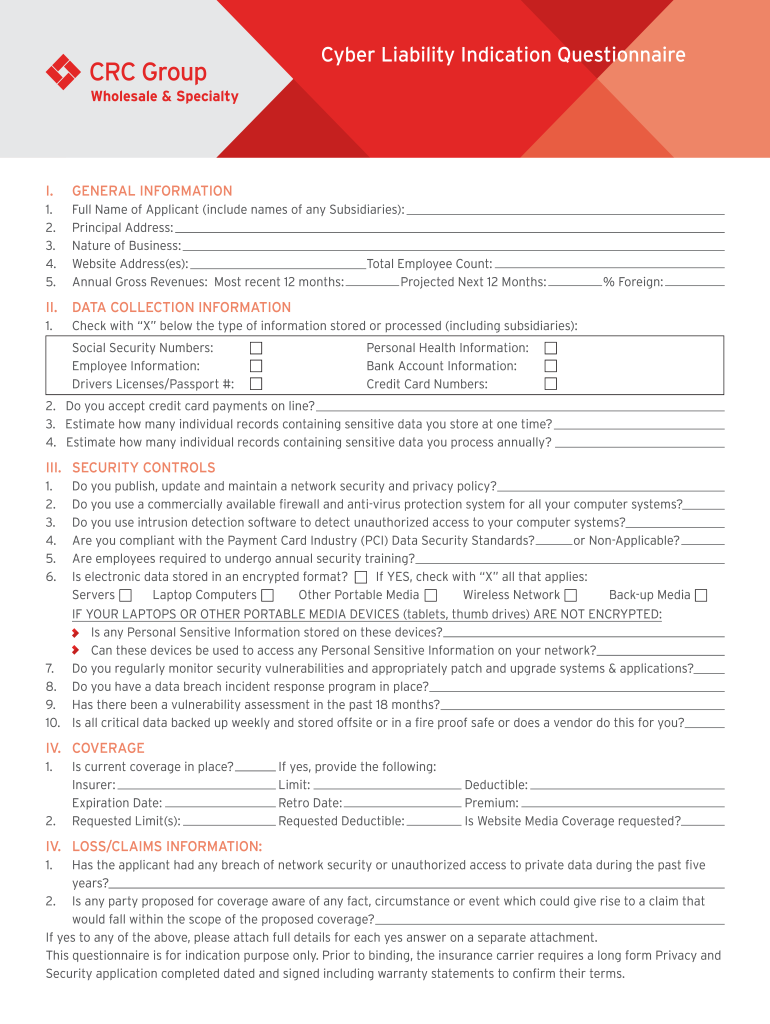
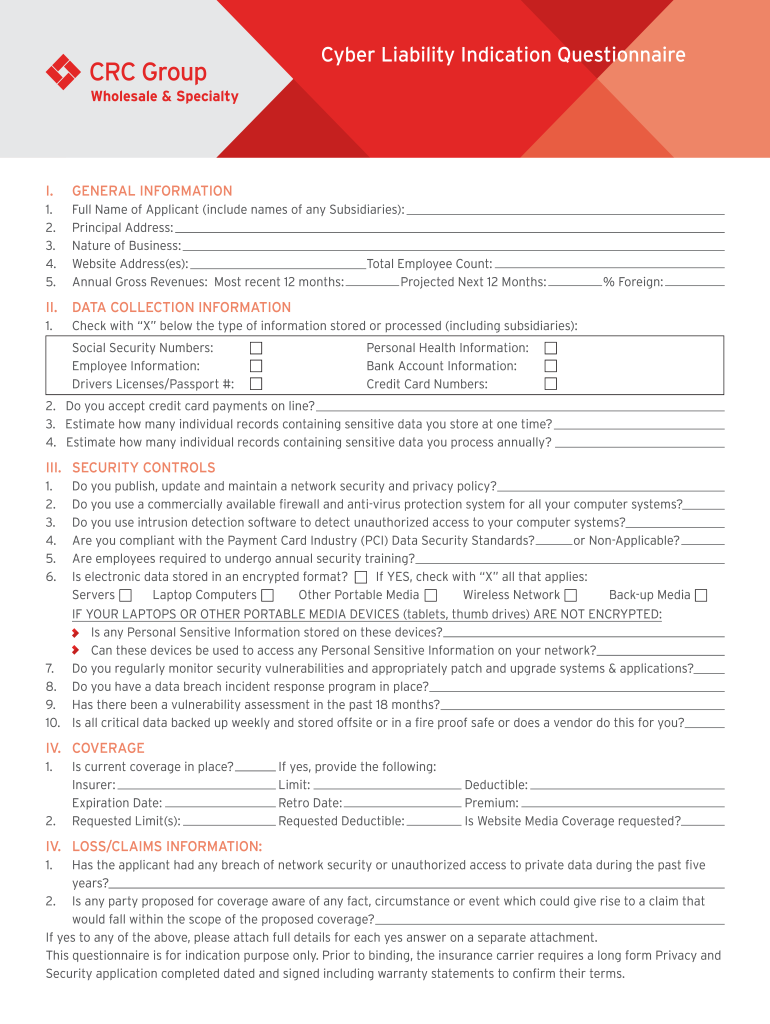
Cyber Liability Indication Questionnaire. GENERAL INFORMATION1.
2.
3.
4.
5. Full Name of Applicant (include names of any Subsidiaries):
Principal Address:
Nature of Business:
Website Address(BS):
Total
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign content analysis of cyber

Edit your content analysis of cyber form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your content analysis of cyber form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing content analysis of cyber online
Use the instructions below to start using our professional PDF editor:
1
Log into your account. It's time to start your free trial.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit content analysis of cyber. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out content analysis of cyber

How to fill out content analysis of cyber
01
To fill out content analysis of cyber, follow these steps:
02
Start by identifying the purpose of the analysis. Determine why you are conducting the content analysis and what you hope to achieve.
03
Define the scope of your analysis. Decide which cyber content you will be analyzing and what aspects of it you are interested in.
04
Collect the cyber content for analysis. Gather relevant articles, documents, reports, social media posts, or any other form of cyber content you need.
05
Create a coding scheme. Develop a set of categories or codes that will help you analyze and classify the content. This could include factors like tone, sentiment, key topics, or any other relevant criteria.
06
Apply the coding scheme to the cyber content. Read or review each piece of content and assign the appropriate code(s) according to your coding scheme.
07
Analyze the coded data. Once all the content has been coded, you can analyze the patterns, trends, or relationships within the data using various statistical or qualitative methods.
08
Interpret the findings. Draw conclusions from your analysis and interpret the meaning or significance of the patterns you have identified.
09
Report the results. Document your findings in a clear and concise manner, providing a detailed report or presentation that highlights the key insights of the content analysis.
10
Review and validate your analysis. Double-check your analysis to ensure accuracy and consider seeking feedback or input from other experts in the cyber field.
11
Take action based on the analysis. Use the insights and information gained from the content analysis to inform decision-making, strategy development, or any other relevant actions.
12
Remember to remain objective and unbiased throughout the content analysis process.
Who needs content analysis of cyber?
01
Content analysis of cyber is beneficial for various individuals, organizations, and researchers involved in cybersecurity, information technology, or digital space. Some examples of who may need content analysis of cyber include:
02
- Cybersecurity experts or analysts who want to understand patterns, trends, or threats in cyber content to enhance security measures or develop effective countermeasures.
03
- Government agencies or law enforcement bodies that monitor cyber activities or investigate cyber crimes. Content analysis can help them identify potential risks, criminal activities, or perpetrators.
04
- Digital marketing or social media professionals who want to analyze cyber content to gain insights into customer behavior, sentiment, or trends for marketing strategies or brand protection.
05
- Researchers or academics studying cyber behavior, cyber propaganda, or online communication. Content analysis can provide valuable data for their studies and contribute to the advancement of knowledge in the field.
06
- Journalists or media organizations interested in reporting on cyber issues or cyber-related events. Content analysis can help them analyze and understand online narratives, disinformation campaigns, or emerging cyber threats.
07
- Businesses or organizations that want to assess their online presence, reputation, or brand image. Content analysis can provide valuable feedback on customer perception, market positioning, or potential vulnerabilities.
08
These are just a few examples, and content analysis of cyber can be relevant for anyone seeking deeper insights or understanding of cyber-related content.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send content analysis of cyber to be eSigned by others?
When you're ready to share your content analysis of cyber, you can send it to other people and get the eSigned document back just as quickly. Share your PDF by email, fax, text message, or USPS mail. You can also notarize your PDF on the web. You don't have to leave your account to do this.
How do I execute content analysis of cyber online?
pdfFiller has made it easy to fill out and sign content analysis of cyber. You can use the solution to change and move PDF content, add fields that can be filled in, and sign the document electronically. Start a free trial of pdfFiller, the best tool for editing and filling in documents.
Can I edit content analysis of cyber on an Android device?
You can edit, sign, and distribute content analysis of cyber on your mobile device from anywhere using the pdfFiller mobile app for Android; all you need is an internet connection. Download the app and begin streamlining your document workflow from anywhere.
What is content analysis of cyber?
Content analysis of cyber refers to the systematic examination of digital content and data to identify patterns, trends, and insights related to cyber activities, often used for security assessments and compliance.
Who is required to file content analysis of cyber?
Organizations and entities that engage in cyber activities, particularly those that handle sensitive information or are subject to regulatory requirements, are typically required to file content analysis of cyber.
How to fill out content analysis of cyber?
To fill out content analysis of cyber, organizations should gather relevant data, utilize appropriate tools or templates, document findings systematically, and ensure compliance with regulatory standards.
What is the purpose of content analysis of cyber?
The purpose of content analysis of cyber is to enhance understanding of cyber risks, improve security measures, ensure compliance with regulations, and inform decision-making processes within organizations.
What information must be reported on content analysis of cyber?
Information that must be reported includes data on cyber incidents, vulnerabilities, response measures, risk assessments, and any actions taken to mitigate cyber threats.
Fill out your content analysis of cyber online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Content Analysis Of Cyber is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















