Get the free A 'massive' hacking attack has hit government websites in ... - andrepiolat csf bc
Show details
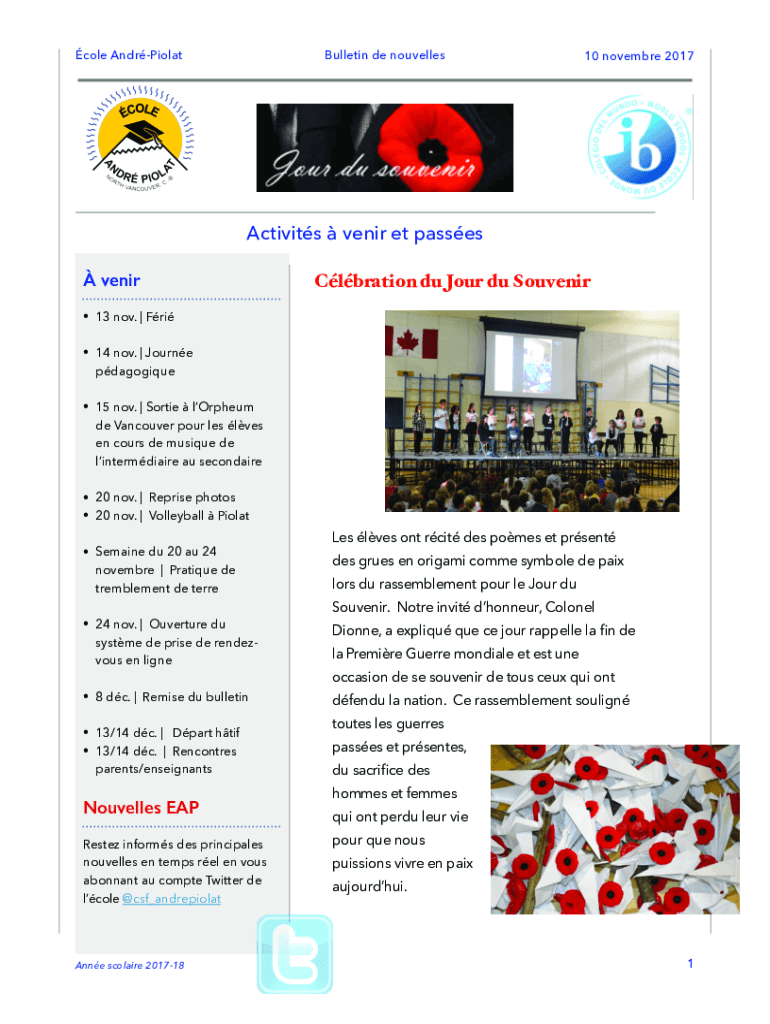
Cole AndrPiolatBulletin de nouvelles10 November 2017Activits senior ET passes venirClbration Du Four Du Souvenir 13 Nov. | Fri 14 Nov. | Journepdagogique 15 Nov. | Sortie morpheme Vancouver pour LES
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign a massive hacking attack

Edit your a massive hacking attack form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your a massive hacking attack form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing a massive hacking attack online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit a massive hacking attack. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
It's easier to work with documents with pdfFiller than you could have ever thought. You can sign up for an account to see for yourself.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out a massive hacking attack

How to fill out a massive hacking attack
01
Identify the target system or network that you want to attack.
02
Conduct thorough reconnaissance to gather information about the target, such as vulnerabilities, weak points, and potential entry points.
03
Exploit any vulnerabilities found in the target system or network to gain unauthorized access.
04
Use various hacking techniques to maintain persistence within the target system or network, ensuring that your access remains undetected.
05
Escalate privileges to gain higher levels of access, allowing you to control and manipulate the target system or network more effectively.
06
Launch a series of coordinated attacks, such as SQL injections, cross-site scripting (XSS), or Distributed Denial of Service (DDoS) attacks, to disrupt or compromise the target system or network.
07
Use social engineering tactics to trick authorized users into revealing sensitive information or granting access privileges.
08
Cover your tracks by clearing any traces of your activities and avoiding detection by security measures or monitoring systems.
09
Continuously adapt and update your attack techniques to bypass any countermeasures implemented by the target system or network.
10
Repeat the steps above as necessary to achieve your hacking objectives.
Who needs a massive hacking attack?
01
Various parties might have motives to conduct a massive hacking attack, including:
02
- Cybercriminals seeking financial gain through theft of sensitive data, intellectual property, or financial resources.
03
- Nation-state actors engaging in cyber warfare or espionage to gain a competitive advantage or weaken their adversaries.
04
- Hacktivist groups aiming to promote a specific cause or ideology by disrupting or exposing targeted organizations or governments.
05
- Independent hackers looking for recognition or reputation within the hacking community.
06
- Security professionals or ethical hackers performing authorized penetration testing to identify vulnerabilities and strengthen defenses.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit a massive hacking attack in Chrome?
Install the pdfFiller Google Chrome Extension to edit a massive hacking attack and other documents straight from Google search results. When reading documents in Chrome, you may edit them. Create fillable PDFs and update existing PDFs using pdfFiller.
Can I create an electronic signature for the a massive hacking attack in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your a massive hacking attack in minutes.
How do I fill out the a massive hacking attack form on my smartphone?
Use the pdfFiller mobile app to fill out and sign a massive hacking attack on your phone or tablet. Visit our website to learn more about our mobile apps, how they work, and how to get started.
What is a massive hacking attack?
A massive hacking attack is a large-scale cyber attack that targets a system or network to steal data, disrupt operations, or cause damage.
Who is required to file a massive hacking attack?
Any individual or organization that experiences a massive hacking attack is required to file a report.
How to fill out a massive hacking attack?
To fill out a report on a massive hacking attack, provide details about the incident, including the nature of the attack, impact on the system, and any steps taken to address it.
What is the purpose of a massive hacking attack?
The purpose of a massive hacking attack can vary, but it is often carried out to gain unauthorized access to sensitive information, disrupt operations, or cause financial harm.
What information must be reported on a massive hacking attack?
The report on a massive hacking attack must include details about the attack, impact on the system, data compromised, and any remediation efforts.
Fill out your a massive hacking attack online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
A Massive Hacking Attack is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















