Get the free Cyber Asset Security Training Handbook for Contractors
Show details
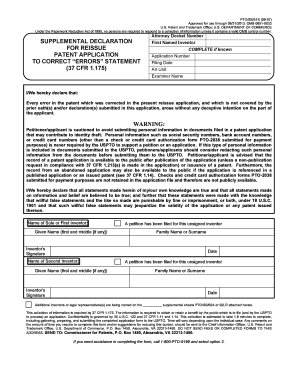
CIP Training for Contractors Instructions A copy of this document must be completed for every contractor employee who has authorized CIP access. The contractors supervisor or manager must sign the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber asset security training

Edit your cyber asset security training form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyber asset security training form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cyber asset security training online
To use the professional PDF editor, follow these steps below:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit cyber asset security training. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber asset security training

How to fill out cyber asset security training
01
Step 1: Identify the specific cyber assets that need to be protected.
02
Step 2: Determine the appropriate level of security training needed based on the sensitivity of the cyber assets.
03
Step 3: Develop a comprehensive training program that covers topics such as identifying threats, practicing safe online behavior, and responding to security incidents.
04
Step 4: Schedule regular training sessions for employees to ensure ongoing awareness and compliance with security protocols.
05
Step 5: Monitor and evaluate the effectiveness of the training program to make necessary adjustments and improvements.
Who needs cyber asset security training?
01
Employees who have access to sensitive information or systems
02
IT professionals responsible for managing and securing cyber assets
03
Managers and executives who oversee cybersecurity operations
04
Contractors and third-party vendors who work with sensitive data
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit cyber asset security training in Chrome?
Adding the pdfFiller Google Chrome Extension to your web browser will allow you to start editing cyber asset security training and other documents right away when you search for them on a Google page. People who use Chrome can use the service to make changes to their files while they are on the Chrome browser. pdfFiller lets you make fillable documents and make changes to existing PDFs from any internet-connected device.
Can I sign the cyber asset security training electronically in Chrome?
You can. With pdfFiller, you get a strong e-signature solution built right into your Chrome browser. Using our addon, you may produce a legally enforceable eSignature by typing, sketching, or photographing it. Choose your preferred method and eSign in minutes.
How do I edit cyber asset security training on an iOS device?
No, you can't. With the pdfFiller app for iOS, you can edit, share, and sign cyber asset security training right away. At the Apple Store, you can buy and install it in a matter of seconds. The app is free, but you will need to set up an account if you want to buy a subscription or start a free trial.
What is cyber asset security training?
Cyber asset security training is specialized training focused on protecting and securing digital assets from cyber threats.
Who is required to file cyber asset security training?
All employees who have access to sensitive digital information are required to complete cyber asset security training.
How to fill out cyber asset security training?
Employees can fill out cyber asset security training by attending in-person or online training sessions and completing any required assessments or quizzes.
What is the purpose of cyber asset security training?
The purpose of cyber asset security training is to educate employees on best practices for preventing cyber attacks and keeping digital assets secure.
What information must be reported on cyber asset security training?
Information reported on cyber asset security training may include employee names, completion dates, training materials used, and assessment scores.
Fill out your cyber asset security training online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Asset Security Training is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.