Get the free Cyber Investigation Technology (CYIT.S.AAS)
Show details
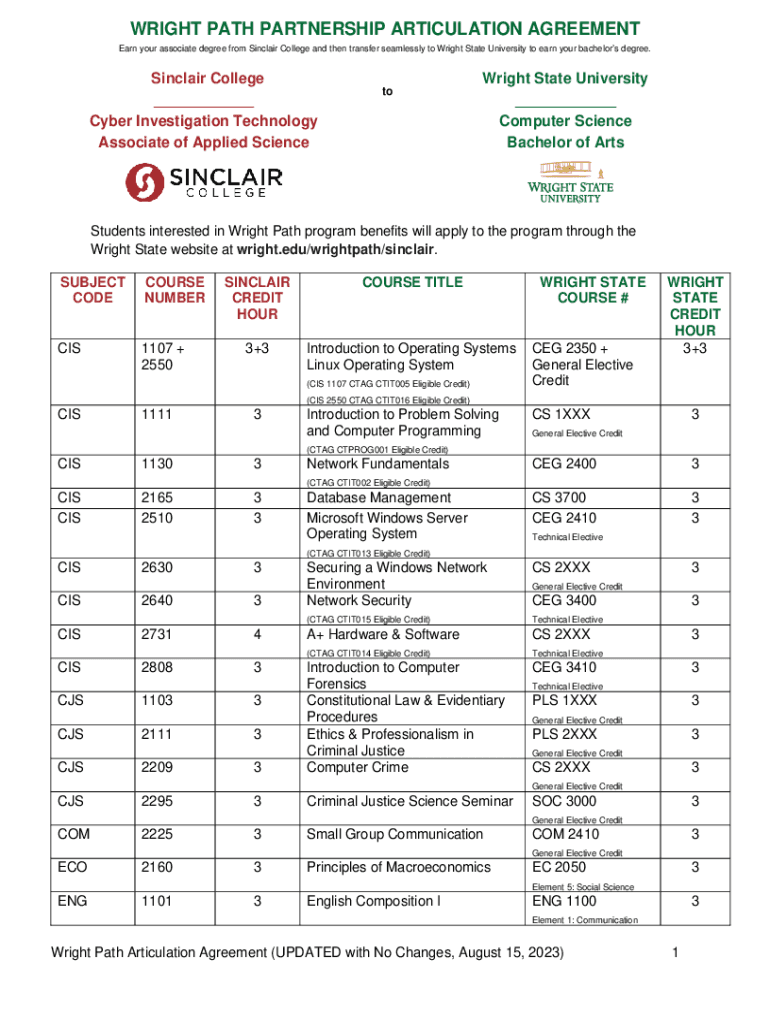
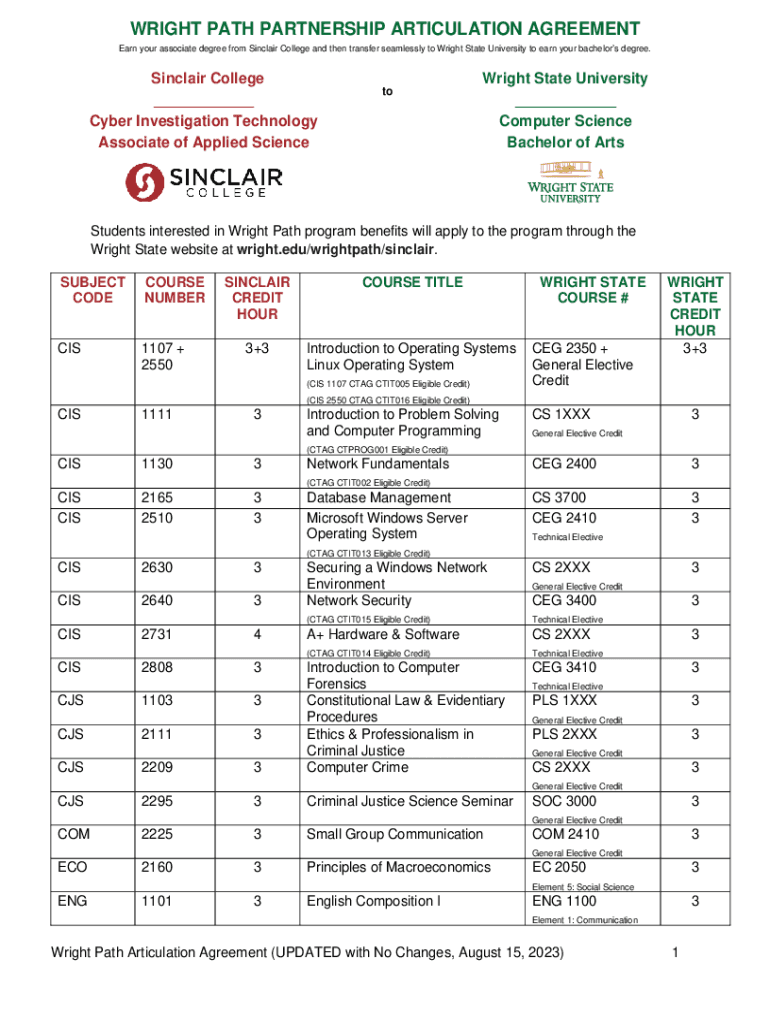
WRIGHT PATH PARTNERSHIP ARTICULATION AGREEMENT Earn your associate degree from Sinclair College and then transfer seamlessly to Wright State University to earn your bachelors degree. Sinclair College
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cyber investigation technology cyitsaas

Edit your cyber investigation technology cyitsaas form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cyber investigation technology cyitsaas form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cyber investigation technology cyitsaas online
To use the professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit cyber investigation technology cyitsaas. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cyber investigation technology cyitsaas

How to fill out cyber investigation technology cyitsaas
01
To fill out cyber investigation technology cyitsaas, follow these steps:
02
Start by gathering all the necessary information related to the cyber investigation.
03
Identify the specific details of the cyber incident or crime that needs to be investigated.
04
Determine the scope and objectives of the investigation to define the goals.
05
Use the cyitsaas platform or tool to input relevant information, such as timestamps, IP addresses, and evidence collected.
06
Follow the guidelines and instructions provided by the cyitsaas tool to ensure accurate and thorough documentation.
07
Organize the information in a systematic manner, such as categorizing evidence, suspects, and incidents.
08
Cross-reference and link related pieces of information to establish connections and patterns.
09
Review and validate the information entered to eliminate any errors or inconsistencies.
10
Generate reports and summaries using the cyitsaas tool, highlighting key findings and supporting evidence.
11
Regularly update and maintain the cyitsaas database with new information as the investigation progresses.
12
Collaborate with other investigators or agencies using the cyitsaas platform to share findings and insights.
13
Continuously monitor and analyze the collected data to uncover new leads or patterns.
14
Follow legal and ethical procedures throughout the investigation process.
15
Finally, securely store and archive the digital evidence to maintain its integrity and admissibility in legal proceedings.
Who needs cyber investigation technology cyitsaas?
01
Cyber investigation technology cyitsaas is needed by:
02
- Law enforcement agencies and cybercrime units to investigate and solve cybercrimes.
03
- Government organizations to protect critical infrastructure and national security.
04
- Private cybersecurity firms and consultants to provide investigative services to clients.
05
- Enterprises and businesses to respond to cybersecurity incidents, identify breaches, and prevent future attacks.
06
- Digital forensics experts and investigators to streamline and enhance their investigative processes.
07
- Legal professionals involved in cybercrime cases to gather evidence and support legal proceedings.
08
- Education and research institutions to study and understand cybersecurity threats and trends.
09
- Ethical hackers and penetration testers to identify vulnerabilities and strengthen defenses.
10
- Individuals or organizations looking to enhance their cybersecurity skills and knowledge.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make changes in cyber investigation technology cyitsaas?
pdfFiller not only allows you to edit the content of your files but fully rearrange them by changing the number and sequence of pages. Upload your cyber investigation technology cyitsaas to the editor and make any required adjustments in a couple of clicks. The editor enables you to blackout, type, and erase text in PDFs, add images, sticky notes and text boxes, and much more.
How do I make edits in cyber investigation technology cyitsaas without leaving Chrome?
cyber investigation technology cyitsaas can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
How do I fill out cyber investigation technology cyitsaas on an Android device?
Use the pdfFiller mobile app and complete your cyber investigation technology cyitsaas and other documents on your Android device. The app provides you with all essential document management features, such as editing content, eSigning, annotating, sharing files, etc. You will have access to your documents at any time, as long as there is an internet connection.
What is cyber investigation technology cyitsaas?
Cyber Investigation Technology SaaS (CYITSAAS) refers to software-as-a-service solutions designed to assist in cyber investigations, enabling organizations to analyze, detect, and respond to cyber threats effectively.
Who is required to file cyber investigation technology cyitsaas?
Organizations that utilize CYITSAAS for cyber investigations, particularly those dealing with sensitive data or in regulated industries, are typically required to file.
How to fill out cyber investigation technology cyitsaas?
Fill out CYITSAAS by providing relevant organizational details, specifying the type of investigation, and submitting the required logs and evidence in the designated format.
What is the purpose of cyber investigation technology cyitsaas?
The purpose of CYITSAAS is to streamline the process of cyber investigations, enhance detection capabilities, and provide actionable insights to mitigate cyber threats.
What information must be reported on cyber investigation technology cyitsaas?
Information that must be reported includes the nature of the incident, affected systems, timelines of events, and any evidence collected during the investigation.
Fill out your cyber investigation technology cyitsaas online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cyber Investigation Technology Cyitsaas is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.