Get the free Automated Malware Analysis Report for http://tonkawacasinos.com
Show details
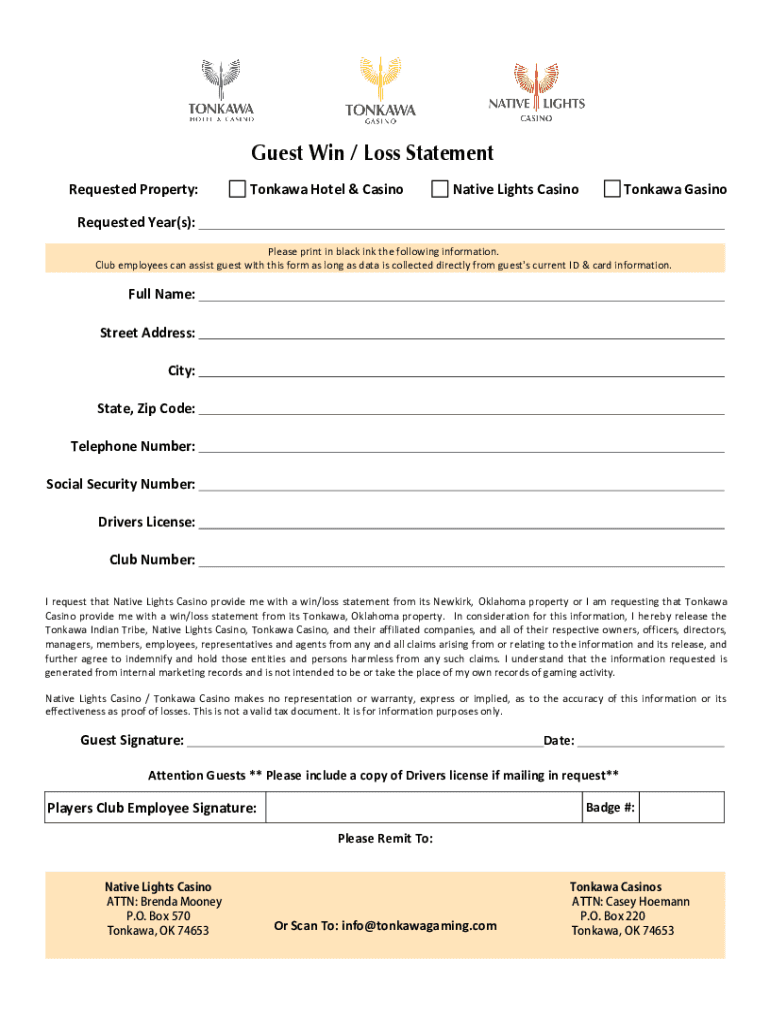
Guest Win / Loss Statement
Requested Property:Tonkawa Hotel & CasinoNative Lights CasinoTonkawa GasinoRequested Year(s):Please print in black ink the following information.Club employees can assist guest with this form as long as data is collected directly from guest\'s current ID & card information.Full Name:Street Address:City:State, Zip Code:Telephone Number:Social Security Number:Drivers License:Club Number:I request that Native Lights Casino provide me with a win/loss statement from its...
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign automated malware analysis report

Edit your automated malware analysis report form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your automated malware analysis report form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing automated malware analysis report online
To use our professional PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit automated malware analysis report. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Try it for yourself by creating an account!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out automated malware analysis report

How to fill out automated malware analysis report
01
To fill out an automated malware analysis report, follow these steps:
02
Begin by collecting all the necessary information about the malware sample being analyzed, such as file name, file hash, and any available metadata.
03
Clearly state the purpose of the analysis report, whether it is for research purposes, incident response, or forensic investigation.
04
Provide a detailed description of the malware, including its behavior, functionality, and any indicators of compromise (IOCs) observed.
05
Include information about the source or origin of the malware, if known, and any relevant context or background.
06
Document the analysis methodology used, such as the tools, techniques, and environments employed for analysis.
07
Present the results of the analysis, including any identified malicious behavior, communication channels, resource usage, or impact on the system.
08
Share any detected vulnerabilities or weaknesses in the analyzed malware.
09
Include information about any remediation or mitigation steps that can be taken to protect against or remove the malware.
10
Clearly organize the report using appropriate headings, sections, and bullet points for better readability.
11
End the report with a conclusion or summary of key findings and recommendations for further actions.
12
Remember to regularly update and review the automated malware analysis report template to adapt to evolving threats and new analysis techniques.
Who needs automated malware analysis report?
01
Automated malware analysis reports are valuable for various individuals and organizations including:
02
- Cybersecurity researchers and analysts who aim to understand the behavior and capabilities of different malware strains.
03
- Incident response teams who need to identify and contain malware in their network or systems.
04
- Cyber threat intelligence providers who collect and disseminate information about emerging threats and attack techniques.
05
- Security operations centers (SOCs) and managed security service providers (MSSPs) who utilize automated analysis reports for continuous monitoring and threat hunting.
06
- Law enforcement agencies and forensic investigators who investigate cybercrimes and use the analysis reports as evidence for prosecutions.
07
- Software developers and vendors who want to identify and address vulnerabilities in their products.
08
- IT administrators and system administrators who seek to protect their networks and systems from malware infections.
09
In summary, anyone involved in cybersecurity, incident response, threat intelligence, or software development can benefit from automated malware analysis reports.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make edits in automated malware analysis report without leaving Chrome?
Install the pdfFiller Google Chrome Extension in your web browser to begin editing automated malware analysis report and other documents right from a Google search page. When you examine your documents in Chrome, you may make changes to them. With pdfFiller, you can create fillable documents and update existing PDFs from any internet-connected device.
How can I fill out automated malware analysis report on an iOS device?
In order to fill out documents on your iOS device, install the pdfFiller app. Create an account or log in to an existing one if you have a subscription to the service. Once the registration process is complete, upload your automated malware analysis report. You now can take advantage of pdfFiller's advanced functionalities: adding fillable fields and eSigning documents, and accessing them from any device, wherever you are.
Can I edit automated malware analysis report on an Android device?
You can make any changes to PDF files, like automated malware analysis report, with the help of the pdfFiller Android app. Edit, sign, and send documents right from your phone or tablet. You can use the app to make document management easier wherever you are.
What is automated malware analysis report?
An automated malware analysis report is a document generated by automated tools that analyze malware samples to provide insights about their behavior, characteristics, and potential threats.
Who is required to file automated malware analysis report?
Organizations and individuals who engage in cybersecurity activities, particularly those analyzing malware for security purposes, are typically required to file automated malware analysis reports.
How to fill out automated malware analysis report?
To fill out an automated malware analysis report, users should input relevant information about the malware sample, including the sample's hash, behavioral characteristics, and any detected threats as provided by the analysis tool.
What is the purpose of automated malware analysis report?
The purpose of an automated malware analysis report is to document the findings of malware analysis for further investigation, sharing with stakeholders, and improving defensive measures against computer threats.
What information must be reported on automated malware analysis report?
The report must include details such as the malware specimen's hash value, identified behavior patterns, any communication protocols used, file names, and any detected indicators of compromise (IoCs).
Fill out your automated malware analysis report online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Automated Malware Analysis Report is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















