Get the free Contractor Privacy & Security Incident Report
Get, Create, Make and Sign contractor privacy security incident



Editing contractor privacy security incident online
Uncompromising security for your PDF editing and eSignature needs
How to fill out contractor privacy security incident

How to fill out contractor privacy security incident
Who needs contractor privacy security incident?
Understanding the Contractor Privacy Security Incident Form
Understanding the Contractor Privacy Security Incident Form
The Contractor Privacy Security Incident Form is a structured document designed to report and manage privacy-related incidents involving contractors. Its primary purpose is to ensure that any potential breaches of sensitive data are documented, assessed, and acted upon swiftly to mitigate risk and comply with regulations. These forms serve as vital tools for maintaining transparency and accountability within organizations, especially as they manage contractor relationships that may involve access to confidential data.
Managing privacy incidents effectively is critical in an age where data breaches can lead to severe reputational damage and regulatory penalties. By standardizing the reporting process through this form, organizations can respond more effectively, ensuring that data subjects are protected and that legal obligations are met.
Definitions and key concepts
A privacy incident refers to any unauthorized access, use, or disclosure of personal information, whether intentional or accidental. Examples of privacy incidents include lost or stolen devices that contain sensitive data, unauthorized access to data by contractors, or inadvertent sharing of confidential information. Understanding what constitutes a privacy incident is crucial for effective reporting and response.
A data breach takes these incidents further, often involving the release of sensitive information to unauthorized parties. It can have serious implications, including identity theft, financial loss, and damage to trust. Sensitive data, in this context, includes Personally Identifiable Information (PII), health records, or financial details, which necessitate heightened protection.
Preparing for incident reporting
Anyone who manages sensitive data within an organization or has been affected by a potential privacy incident should utilize the Contractor Privacy Security Incident Form. This includes contractors, team leaders, and compliance officers. Pre-incident documentation is crucial, as it provides context and supporting evidence for the reported issue.
Stakeholders involved in the reporting process may include IT security teams, human resources personnel, legal advisors, and executive management. Each party plays a critical role in ensuring that incidents are reported swiftly and managed effectively.
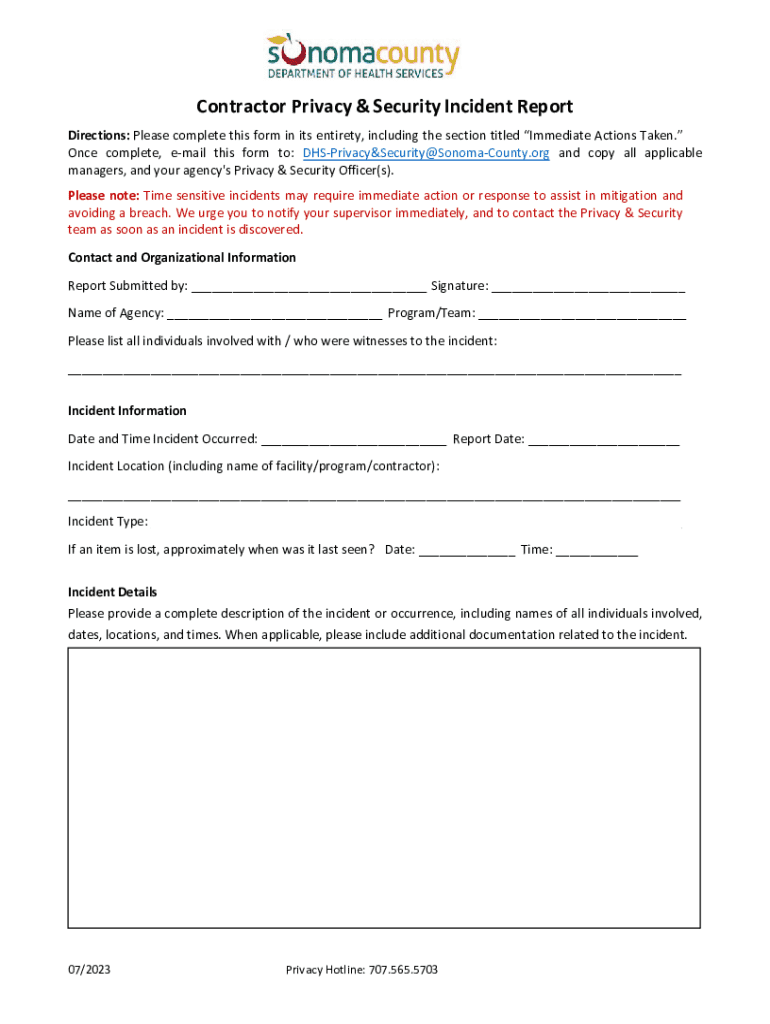
Completing the Contractor Privacy Security Incident Form
Filling out the Contractor Privacy Security Incident Form involves several step-by-step actions to ensure completeness and accuracy. The first step is identifying the incident type, whether it involves unauthorized access, misuse of data, or a loss of sensitive information.
Next, document the incident details meticulously. This should include dates, times, how the incident was discovered, stakeholders involved, and the type of sensitive data at risk. Notifying relevant teams, such as IT and legal, is essential as they can provide immediate assistance and initiate further investigation.
While filling out the form, avoid common pitfalls such as providing incomplete data, failing to report within designated timelines, or neglecting to follow up. Adhering to best practices, including thoroughness and clarity, enhances the form's effectiveness.
Submission and follow-up procedures
Once the Contractor Privacy Security Incident Form is completed, it must be submitted following established organizational protocols. Submission options may include email, internal databases, or via designated online platforms. The method of submission should be clear and align with your organization's policies.
After submission, tracking is vital. Expect an acknowledgment of receipt, and be aware of the case number assigned for reference. Understanding the timeline for the organization’s incident response process helps manage expectations and ensures that the situation is handled promptly.
Response and mitigation steps
Immediate actions following the incident report can significantly affect the outcome. These actions may include isolating affected systems to prevent further breaches, initiating a risk assessment, and ensuring that all sensitive data is secured. Proper investigation procedures should then be carried out to establish the cause of the incident and identify any lapses in protocol.
It’s imperative to document all findings during the investigation to create a clear record for potential legal proceedings and further internal reviews. Additionally, develop communication protocols to inform affected parties and stakeholders about the breach transparently.
Compliance and legal considerations
Organizations must adhere to relevant laws and regulations when handling privacy incidents. These laws could be industry-specific (like HIPAA for healthcare) or general privacy laws (like GDPR for organizations collecting data from EU residents). Contractors, as part of the organizational fabric, are equally responsible for upholding these legal standards to protect sensitive data.
Failure to comply with privacy regulations can result in heavy penalties, legal repercussions, and significant reputational damage. Understanding these obligations empowers contractors to act responsibly and facilitates a proactive approach to incident management.
Post-incident analysis and reporting
Conducting a thorough breach analysis is essential for improving future responses. This involves reviewing what occurred, how the incident was managed, and identifying areas of vulnerability within your data handling processes. This retrospective analysis not only strengthens your current protocols but also aids in developing comprehensive training resources for staff.
Evaluating findings and sharing them with leadership and stakeholders ensures that everyone in the organization is aware of the challenges faced. This transparency can foster a culture of continuous improvement in privacy incident management.
Training and resources for continuous improvement
Regular training for teams on privacy incident response is vital for ensuring everyone understands their roles and responsibilities. This training should cover not just what to do when an incident occurs but also preventative measures that can reduce the chances of incident occurrence.
Moreover, implementing best practices in privacy incident response and utilizing resources such as interactive workshops or e-learning can empower employees. Consider adopting tools tailored for effective incident management, enabling seamless reporting and response tracking.
Additional support available
For organizations looking to enhance their compliance framework, accessing tools such as pdfFiller’s document management solutions can streamline the process of filling out and managing the Contractor Privacy Security Incident Form. These solutions allow for easy document collaboration and ensure that all parties involved are aligned.
Utilizing cloud-based platforms supports real-time collaboration, ensuring that incident reports can be edited and shared instantly among stakeholders. For additional expertise in handling privacy incidents, contacting specialized support teams can also provide further guidance.
Related document templates and tools
Beyond the Contractor Privacy Security Incident Form, pdfFiller offers various document templates that support organizations in managing privacy incidents and related compliance efforts. Integrating these templates within broader security policies can create a robust framework for incident management.
Interactive tools also enhance document management by providing fillable fields and guided prompts, making it easier for teams to navigate through complex forms while reducing the risk of human error in documentation.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find contractor privacy security incident?
How do I edit contractor privacy security incident on an Android device?
How do I complete contractor privacy security incident on an Android device?
What is contractor privacy security incident?
Who is required to file contractor privacy security incident?
How to fill out contractor privacy security incident?
What is the purpose of contractor privacy security incident?
What information must be reported on contractor privacy security incident?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.