Get the free End-User Computing Strategy in the United States Marine Corps
Get, Create, Make and Sign end-user computing strategy in
Editing end-user computing strategy in online
Uncompromising security for your PDF editing and eSignature needs
How to fill out end-user computing strategy in
How to fill out end-user computing strategy in
Who needs end-user computing strategy in?
End-user computing strategy in form: A comprehensive guide
Understanding end-user computing (EUC)
End-user computing (EUC) refers to systems and tools that allow end users to create and manage their own computing solutions without extensive IT intervention. This shift aims to empower users to independently fulfill their software needs, favoring user-friendly interfaces and reduced complexity over traditional IT-driven methods.
EUC encompasses a wide range of applications and devices, including personal computers, tablets, smartphones, and cloud-based applications. This contrasts with traditional computing, primarily managed by IT administrators. The primary difference lies in how control and responsibilities are distributed between end users and the IT department.
Components of an end-user computing strategy
An effective EUC strategy aligns with broader business goals while addressing the specific needs of users. Beginning with strategic objectives, organizations should assess their current infrastructure to identify what technologies and systems are in place.
Strategically tailoring EUC initiatives involves not only understanding existing technologies but also capturing user input on their experiences, which can guide adjustments. For a successful assessment, organizations should evaluate gaps in user experience and performance to create a responsive EUC ecosystem.
Developing a form-based approach to EUC
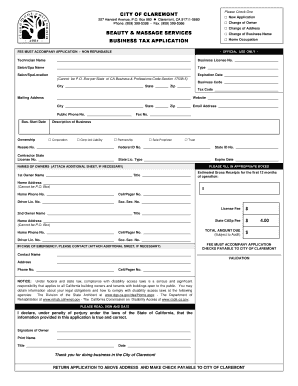
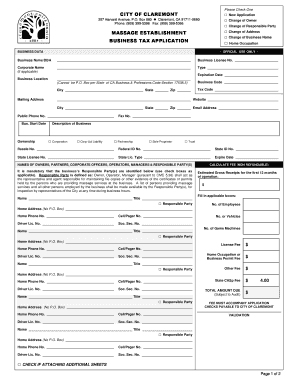
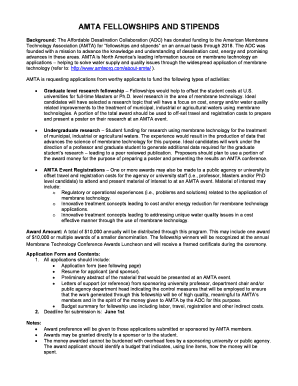
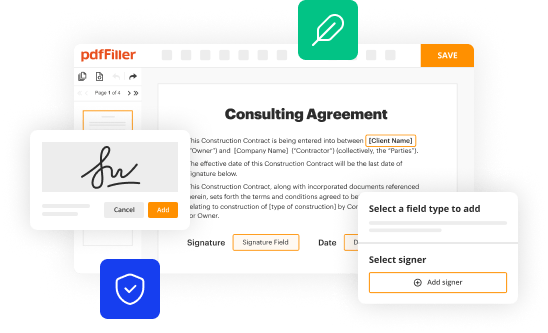
A crucial aspect of developing a robust EUC strategy is the effective management of documents. Streamlining the document creation process enhances productivity, allowing users to generate necessary data without getting bogged down by cumbersome regulations. Utilizing dynamic, fillable forms enables faster collection of information, which is vital in real-time environments.
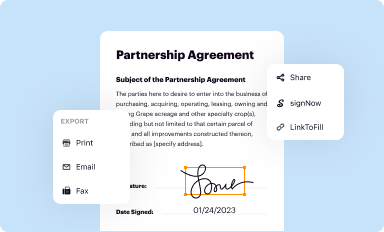
Collaboration is accelerated through the use of integrated form solutions. Tools like pdfFiller offer capabilities for editing, signing, and managing documents efficiently, allowing teams to work in unison, regardless of their physical locations. Integrating eSignatures further facilitates seamless transactions, eliminating the delays of manual processes.
Technology and platform choices in EUC
Selecting the right tools and technologies is pivotal in implementing a successful end-user computing strategy. Current market offerings include a spectrum of cloud-based solutions that often outpace traditional, on-premises setups in terms of flexibility, scalability, and cost-effectiveness.
Organizations must weigh their options by considering the appropriate deployment model, whether it be cloud-based or on-premises. Increasingly, experts advocate for adopting mobile solutions enabling remote access, particularly in industries adapting to hybrid work environments.
Security and compliance in end-user computing
One of the primary concerns with EUC implementations is enhancing security measures and ensuring data privacy. The decentralization of computing resources raises the risk of data breaches and misuse. Organizations must establish robust protocols safeguarding user data and maintaining compliance with industry regulations.
To promote safety, adopting best practices in data integrity is essential. Policies should clarify the use of tools within the organization, mitigating shadow IT risks. Simultaneously, understanding compliance requirements such as GDPR and HIPAA will assist in forming a governance framework that addresses industry mandates.
Enhancing user experience and engagement
Personalization is key to improving user interfaces within EUC solutions. By actively gathering user feedback, organizations can make informed adjustments that elevate the overall user experience. This might involve augmented features based on user necessity or simplifying existing processes to match user expectations.
Fostering collaboration amongst users enhances not only productivity but also engagement. Utilizing tools and features that promote teamwork, such as shared documents or real-time collaboration platforms, creates a unified working environment. Examining case studies from organizations that have successfully implemented these strategies can provide valuable insights.
Operational excellence in end-user computing
Regular maintenance and lifecycle management practices are crucial for ensuring that EUC solutions remain effective over time. Establishing protocols for updates and monitoring system performance metrics will help organizations track the health of their EUC ecosystem.
Budgeting for EUC initiatives requires foresight and strategic planning. Organizations should identify areas for cost optimization by leveraging automation to streamline repetitive tasks, ultimately reducing overhead.
Measuring the success of your EUC strategy
To gauge the efficacy of an EUC strategy, organizations must define key performance indicators (KPIs) reflecting user adoption and overall satisfaction. Tracking metrics provides insights into productivity gains and areas needing improvement.
Emphasizing continuous improvement processes is crucial for long-term success. Employing data-driven insights can help refine strategies, ensuring alignment with evolving user needs and technological trends.
Specific use cases of end-user computing
EUC implementations can vary significantly across industries. In healthcare, EUC tools enable enhanced patient care through efficient record-keeping and real-time data access. Similarly, in finance, effective EUC strategies improve compliance reporting processes, leading to better regulatory adherence.
As organizations transition to remote working, understanding adaptability among the workforce can create efficiencies. Implementing strategies for managing contingent and seasonal workers is imperative, while being proactive about future work environments ensures preparedness.
Risk management in end-user computing
Recognizing common risks and challenges in EUC initiatives is essential for effective risk management. Scalability issues often arise in growing organizations, necessitating proactive planning to accommodate increased user demands without compromising performance.
High maintenance overhead can complicate EUC solutions. A well-defined EUC policy emphasizing user training can mitigate many risks, clarifying roles and responsibilities while fostering a culture of compliance and security awareness.
Future trends and innovations in end-user computing
Anticipating changes in user needs and technology is vital in sustaining an effective EUC strategy. One notable innovation is the rise of zero trust security models, which bolster data protection by limiting access based on user identity rather than location.
Future-proofing your EUC strategy means not only staying updated on the latest technological advancements but also fostering a culture of innovation within your organization. Embracing emerging technologies will further enhance the end-user experience.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send end-user computing strategy in for eSignature?
How do I make changes in end-user computing strategy in?
How do I make edits in end-user computing strategy in without leaving Chrome?
What is end-user computing strategy in?
Who is required to file end-user computing strategy in?
How to fill out end-user computing strategy in?
What is the purpose of end-user computing strategy in?
What information must be reported on end-user computing strategy in?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.