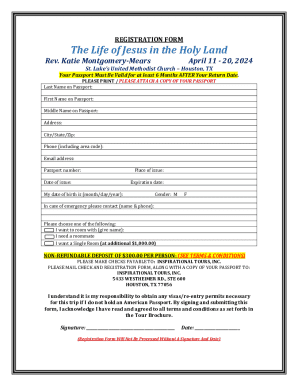
Get the free Covert Botnet Implementation and Defense Against Covert Botnets - digitalcommons usu
Show details
This thesis explores the implementation and defense against covert botnets, focusing on stealthy botnet attacks, existing defense mechanisms, and proposes new methods for combating these threats through
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign covert botnet implementation and

Edit your covert botnet implementation and form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your covert botnet implementation and form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit covert botnet implementation and online
Use the instructions below to start using our professional PDF editor:
1
Log in to your account. Start Free Trial and sign up a profile if you don't have one.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit covert botnet implementation and. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
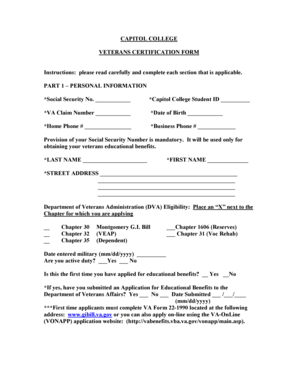
How to fill out covert botnet implementation and

How to fill out covert botnet implementation and
01
Research and gather information on covert botnet technologies.
02
Define the purpose and objectives of the botnet implementation.
03
Choose the appropriate platforms and tools for deployment.
04
Create a secure environment for operation to prevent detection.
05
Develop the botnet code or source the necessary software.
06
Configure the command and control (C&C) infrastructure.
07
Deploy the botnet nodes discreetly on targeted systems.
08
Test the botnet functionalities in a controlled setting.
09
Monitor the botnet's performance and make necessary adjustments.
10
Ensure compliance with ethical and legal standards, evaluating risks involved.
Who needs covert botnet implementation and?
01
Cybersecurity experts for testing and research purposes.
02
Organizations seeking to simulate attacks for defensive strategies.
03
Government agencies involved in cybersecurity operations.
04
Ethical hackers focusing on secure network enhancement.
05
Individuals or groups interested in understanding cyber threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit covert botnet implementation and in Chrome?
Install the pdfFiller Google Chrome Extension to edit covert botnet implementation and and other documents straight from Google search results. When reading documents in Chrome, you may edit them. Create fillable PDFs and update existing PDFs using pdfFiller.
Can I sign the covert botnet implementation and electronically in Chrome?
You certainly can. You get not just a feature-rich PDF editor and fillable form builder with pdfFiller, but also a robust e-signature solution that you can add right to your Chrome browser. You may use our addon to produce a legally enforceable eSignature by typing, sketching, or photographing your signature with your webcam. Choose your preferred method and eSign your covert botnet implementation and in minutes.
How do I fill out covert botnet implementation and on an Android device?
Use the pdfFiller mobile app and complete your covert botnet implementation and and other documents on your Android device. The app provides you with all essential document management features, such as editing content, eSigning, annotating, sharing files, etc. You will have access to your documents at any time, as long as there is an internet connection.
What is covert botnet implementation?
Covert botnet implementation refers to the deployment of malicious software that allows a network of compromised computers, or 'bots,' to be controlled secretly by an attacker, typically for the purposes of executing cybercrimes like DDoS attacks or data theft.
Who is required to file covert botnet implementation?
Individuals or organizations that have deployed or have been affected by a covert botnet implementation, as well as cybersecurity professionals involved in incident reporting, may be required to file regarding such implementations.
How to fill out covert botnet implementation?
To fill out a covert botnet implementation report, one should provide detailed information about the incident, including the nature of the infection, potential vulnerabilities exploited, affected systems, and any actions taken to mitigate the attack.
What is the purpose of covert botnet implementation?
The purpose of covert botnet implementation is primarily malicious, aiming to leverage compromised systems for unauthorized activities without detection, potentially causing significant harm to individuals and organizations.
What information must be reported on covert botnet implementation?
Reported information typically includes the type and scale of the botnet, methods of infection, data compromised, timeline of events, mitigation efforts undertaken, and any indicators of compromise (IOCs) encountered.
Fill out your covert botnet implementation and online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Covert Botnet Implementation And is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.