Get the free Computer Software Security Program for Information Technology
Get, Create, Make and Sign computer software security program
Editing computer software security program online
Uncompromising security for your PDF editing and eSignature needs
How to fill out computer software security program
How to fill out computer software security program
Who needs computer software security program?
Comprehensive Guide to the Computer Software Security Program Form
Overview of computer software security programs
Computer software security encompasses the measures taken to protect software products, applications, and systems from unauthorized access, damage, or attacks. It plays a crucial role in safeguarding sensitive data and ensuring compliance with various regulations defined by the White House Office of Management and Budget (OMB) and sector-specific guidelines.
Given the rising number of cyber threats and their implications, software security programs have evolved into essential protective measures for organizations. These programs not only bolster defenses but also provide frameworks for accountability and transparency in software development. Furthermore, software producers must navigate compliance requirements, including OMB Memoranda M-22 and M-23, to meet government standards for security.
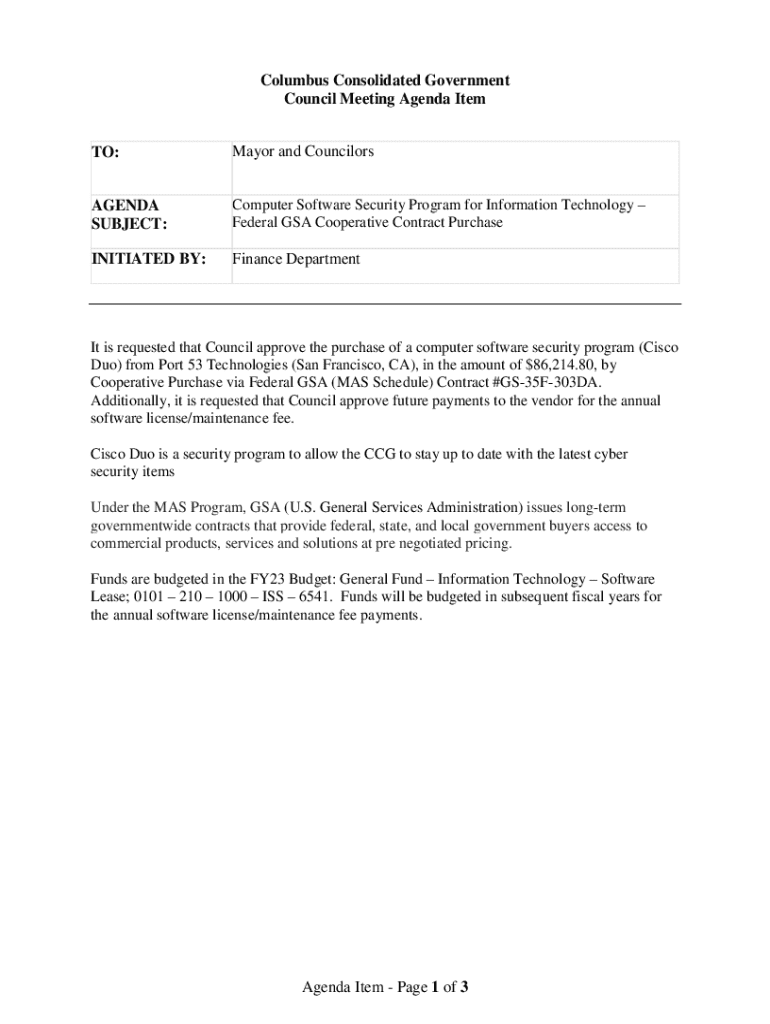
Understanding the computer software security program form
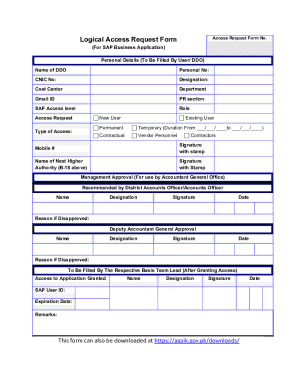
The computer software security program form serves as a comprehensive tool for collating vital information regarding software applications and ensuring adherence to relevant security frameworks. This form plays a critical role in the documentation process, enabling precise record-keeping and facilitating audits and compliance checks.
Primarily, the form aids in gathering essential details that contribute to a software's security posture. Organizations utilize this form to not only report compliance with prescribed security assessments but also to assure stakeholders, including regulatory bodies, that adequate measures are in place to protect sensitive data.
Step-by-step guide to filling the computer software security program form
Before diving into the form, it's essential to prepare adequately to ensure a smooth completion process. First and foremost, gathering necessary documentation before form completion will streamline the data entry workflow. This may include software design specifications, security testing reports, and compliance certifications.
Once the documentation is at hand, conducting an initial software security assessment is crucial. This step not only aids in fulfilling the field requirements, but also provides insights into existing vulnerabilities and areas needing improvement.
Editing and managing the computer software security program form
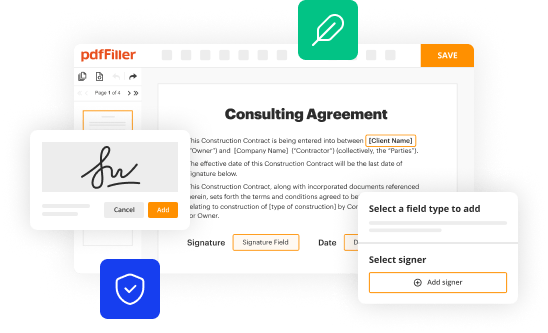
Once the form is filled out, utilizing tools such as pdfFiller can make managing and editing more efficient. pdfFiller provides step-by-step editing instructions that allow users to seamlessly modify their documents as needed, ensuring the information remains accurate and up-to-date.
Additionally, pdfFiller’s collaborative features enable teams to review and make necessary amendments in real-time, fostering an environment of inclusivity and thoroughness in compliance documentation.
Interactive tools provided by pdfFiller
pdfFiller enhances the document management experience by offering interactive features that streamline the process of managing the computer software security program form. Automatic field detection helps users by identifying relevant fields, significantly reducing manual input and potential errors.
Moreover, validation checks within the platform ensure that all necessary fields are completed correctly, minimizing the chances of submission errors. With additional tools for analytics and tracking, organizations can monitor submission status and review compliance metrics effortlessly.
Managing document security and compliance
Establishing robust strategies for continuous security assurance is vital for maintaining compliance and mitigating risks. Regular updates and audits to the software security framework ensure that any vulnerabilities are quickly addressed and rectified. Organizations should also invest in training and awareness programs to keep all personnel informed about best practices in software security.
Legal implications surrounding non-compliance can lead to severe penalties, including fines and reputational damage. Keeping abreast of relevant regulations, particularly omb memoranda detailing software accounting processes and security standards, is critical to avoid these pitfalls.
Troubleshooting common issues with the form
If users encounter technical issues while filling or submitting the computer software security program form, it's essential to identify and resolve these challenges swiftly. Common problems include form loading issues that can usually be resolved by checking internet connectivity or refreshing the browser.
For challenges related to editing or signing, users should leverage the support resources provided by pdfFiller. The FAQ section can be particularly beneficial for quickly identifying solutions to frequent concerns, ensuring a smoother experience.
Real-world applications of the computer software security program form
The application of the computer software security program form is evident across various industries, each facing unique security challenges. For instance, financial institutions often employ such forms to ensure customer data protection standards are met while software developments are underway. Similarly, healthcare sectors utilize these forms to align with HIPAA compliance, ensuring patient information is secured.
Case studies from organizations that have effectively used the computer software security program form highlight the importance of ongoing risk assessment and transparency in compliance processes. Users have reported improvements in compliance readiness and stakeholder confidence.
Future trends in software security and compliance
As technology rapidly evolves, so too do the methodologies behind software security. Emerging technologies such as blockchain and advanced encryption stand to revolutionize how software security is approached, creating innovative ways to protect sensitive data.
Additionally, the advent of artificial intelligence and machine learning introduces new capabilities for threat detection and response, allowing for quicker identification and mitigation of vulnerabilities. Organizations must stay proactive, adapting their compliance requirements in lockstep with technological advancements to ensure ongoing security.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make edits in computer software security program without leaving Chrome?
Can I create an electronic signature for signing my computer software security program in Gmail?
How do I complete computer software security program on an iOS device?
What is computer software security program?
Who is required to file computer software security program?
How to fill out computer software security program?
What is the purpose of computer software security program?
What information must be reported on computer software security program?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.