
Get the free Java Cryptography Architecture - Sharif - ce sharif
Show details
Java Cryptography Architecture 1 of 67 file:///D:/temp%20behnamyou%20can%20delete%20it/jdk1 5 0doc/... Java Cryptography Architecture TM API Specification & Reference Last Modified: 25 July 2004 Introduction
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign java cryptography architecture
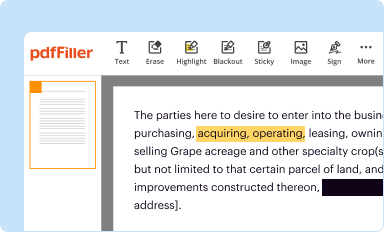
Edit your java cryptography architecture form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
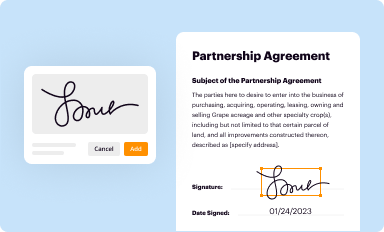
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
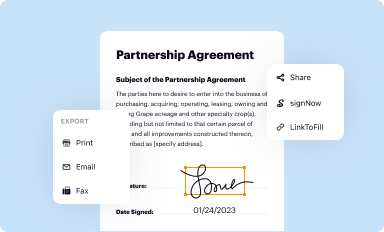
Share your form instantly
Email, fax, or share your java cryptography architecture form via URL. You can also download, print, or export forms to your preferred cloud storage service.
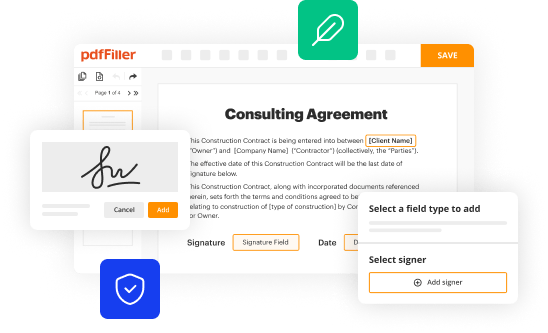
Editing java cryptography architecture online
To use the services of a skilled PDF editor, follow these steps below:
1
Log into your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit java cryptography architecture. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out java cryptography architecture
When it comes to filling out the Java Cryptography Architecture, it is important to have a clear understanding of the process and why it is needed. Here's a point-by-point guide to help you navigate through it:
How to fill out Java Cryptography Architecture:
01
Start by familiarizing yourself with the basic concepts of cryptography. Understanding how encryption and decryption work will enable you to make informed decisions when choosing cryptographic algorithms for your Java application.
02
Identify the specific security requirements of your application. Determine the level of data protection needed and the potential risks associated with unauthorized access. This will guide you in selecting the appropriate cryptographic services and features provided by the Java Cryptography Architecture.
03
Begin implementing the necessary cryptographic functionality in your Java application. This involves utilizing the relevant classes and interfaces provided by the Java Cryptography Architecture, such as KeyStore for managing keys and certificates, Cipher for encryption and decryption operations, SecureRandom for generating secure random numbers, and MessageDigest for hashing data.
04
Ensure that you are using secure and robust cryptographic algorithms. Java provides a wide range of standard algorithms, such as AES, RSA, and SHA, which offer varying levels of security. Consider factors such as performance, compatibility, and industry best practices when making algorithm choices.
05
Keep up with software updates and security patches. The field of cryptography is constantly evolving, and new vulnerabilities and attacks are often discovered. Staying updated with the latest releases of the Java Cryptography Architecture ensures that your implementation remains secure and meets the current cryptographic standards.
Who needs Java Cryptography Architecture:
01
Developers working on applications that handle sensitive data, such as financial institutions, healthcare organizations, and e-commerce platforms, require the Java Cryptography Architecture to protect the confidentiality and integrity of data transmitted and stored.
02
Organizations dealing with regulatory compliance, like those in the financial sector (e.g., banks, insurance companies) or healthcare industry (e.g., hospitals, electronic medical record providers), often need to comply with encryption standards and requirements mandated by regulatory bodies. The Java Cryptography Architecture can help achieve compliance in such cases.
03
Any Java developer looking to ensure data security and privacy in their applications can benefit from employing the Java Cryptography Architecture. Regardless of the industry or specific use case, encryption and other cryptographic techniques are crucial for safeguarding sensitive information.
Remember that the implementation of the Java Cryptography Architecture should be tailored to your specific requirements and utilize appropriate cryptographic practices. Understanding the principles, adhering to best practices, and regularly updating your implementation will help you maintain a secure and reliable application.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my java cryptography architecture directly from Gmail?
You may use pdfFiller's Gmail add-on to change, fill out, and eSign your java cryptography architecture as well as other documents directly in your inbox by using the pdfFiller add-on for Gmail. pdfFiller for Gmail may be found on the Google Workspace Marketplace. Use the time you would have spent dealing with your papers and eSignatures for more vital tasks instead.
How can I edit java cryptography architecture from Google Drive?
Using pdfFiller with Google Docs allows you to create, amend, and sign documents straight from your Google Drive. The add-on turns your java cryptography architecture into a dynamic fillable form that you can manage and eSign from anywhere.
How do I edit java cryptography architecture in Chrome?
Get and add pdfFiller Google Chrome Extension to your browser to edit, fill out and eSign your java cryptography architecture, which you can open in the editor directly from a Google search page in just one click. Execute your fillable documents from any internet-connected device without leaving Chrome.
What is java cryptography architecture?
Java Cryptography Architecture (JCA) defines a framework for working with cryptography operations in Java.
Who is required to file java cryptography architecture?
Developers or organizations working with cryptographic operations in Java are required to follow JCA guidelines.
How to fill out java cryptography architecture?
Java Cryptography Architecture can be implemented by using Java's security APIs and following the JCA documentation.
What is the purpose of java cryptography architecture?
The purpose of JCA is to provide a secure and standardized way to handle cryptographic operations in Java applications.
What information must be reported on java cryptography architecture?
Information regarding the implementation of cryptographic algorithms, key management, and secure communication protocols must be reported on JCA.
Fill out your java cryptography architecture online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Java Cryptography Architecture is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















