Get the free Computer Information Technology Cyber Defense Concentration - ww2 nscc
Show details
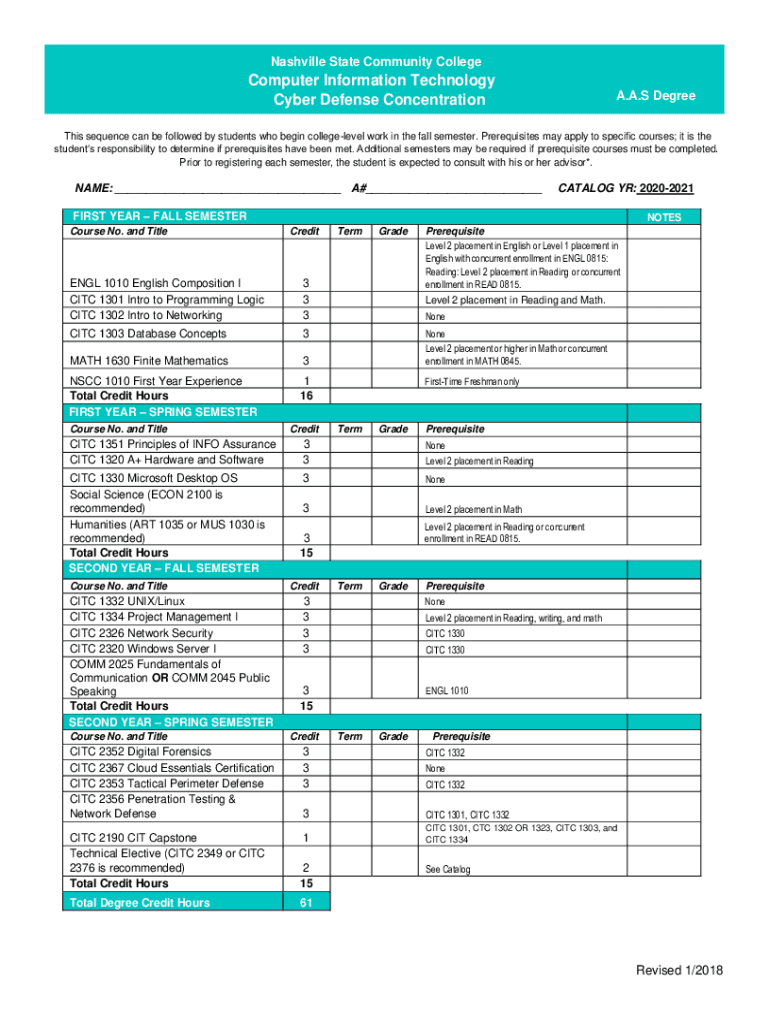
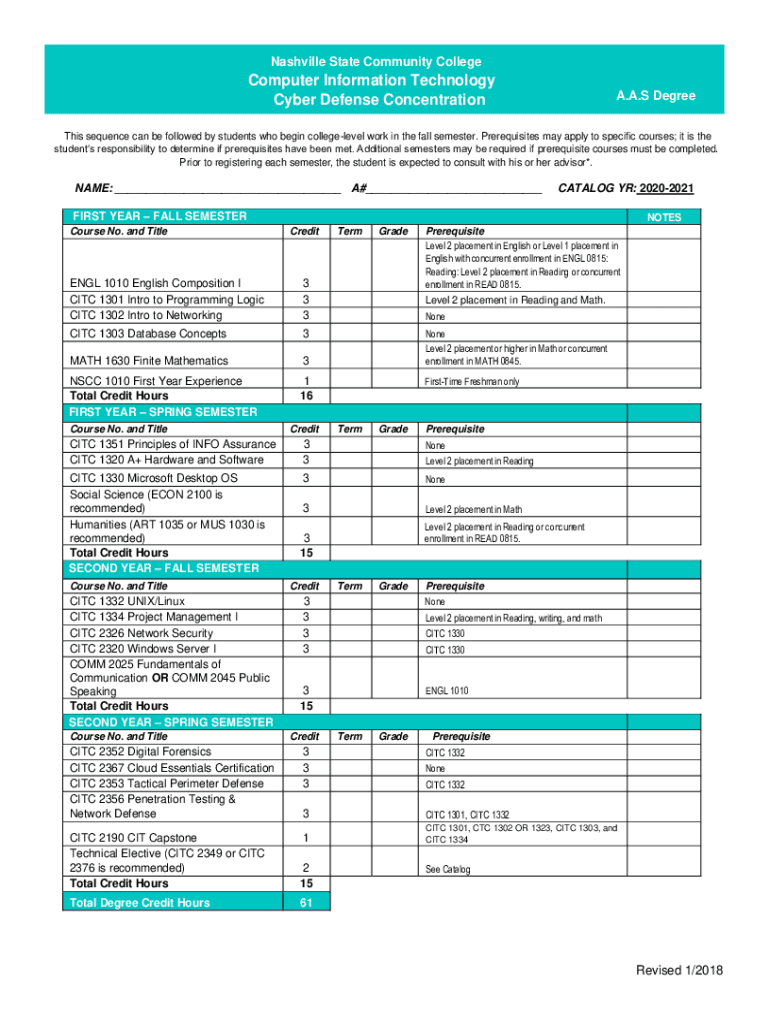
Nashville State Community CollegeComputer Information Technology Cyber Defense Concentration. A. S Degrees sequence can be followed by students who begin college level work in the fall semester. Prerequisites
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign computer information technology cyber

Edit your computer information technology cyber form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your computer information technology cyber form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing computer information technology cyber online
To use the services of a skilled PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit computer information technology cyber. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
Dealing with documents is simple using pdfFiller. Try it right now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out computer information technology cyber

How to fill out computer information technology cyber
01
To fill out computer information technology cyber, follow these steps:
02
Gather all the necessary information such as the computer's make and model, operating system, installed software, and hardware specifications.
03
Start by providing the basic information about the computer including its brand, model, and serial number. This will help identifying the specific machine.
04
Specify the operating system installed on the computer. Include the version and any relevant service packs or updates.
05
List down all the software applications installed on the computer, including their versions. This will help in troubleshooting and software management.
06
Provide details about the computer's hardware specifications such as the processor, RAM, hard drive capacity, and graphics card.
07
Include any additional information related to the computer's network configuration, peripherals, or specialized software used for cyber security purposes.
08
Double-check all the information provided for accuracy and completeness.
09
Save the completed computer information technology cyber form for future reference or sharing with relevant parties.
Who needs computer information technology cyber?
01
Computer information technology cyber is needed by:
02
- Individuals or organizations in the field of computer security to keep a record of cyber security measures and configurations.
03
- IT professionals responsible for managing and maintaining computer systems and networks.
04
- System administrators who need to track the specifications and configurations of computers within their network.
05
- Computer manufacturers and vendors who require accurate information about their products for support purposes.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send computer information technology cyber to be eSigned by others?
Once your computer information technology cyber is ready, you can securely share it with recipients and collect eSignatures in a few clicks with pdfFiller. You can send a PDF by email, text message, fax, USPS mail, or notarize it online - right from your account. Create an account now and try it yourself.
Can I sign the computer information technology cyber electronically in Chrome?
Yes. By adding the solution to your Chrome browser, you can use pdfFiller to eSign documents and enjoy all of the features of the PDF editor in one place. Use the extension to create a legally-binding eSignature by drawing it, typing it, or uploading a picture of your handwritten signature. Whatever you choose, you will be able to eSign your computer information technology cyber in seconds.
How do I complete computer information technology cyber on an Android device?
Use the pdfFiller mobile app and complete your computer information technology cyber and other documents on your Android device. The app provides you with all essential document management features, such as editing content, eSigning, annotating, sharing files, etc. You will have access to your documents at any time, as long as there is an internet connection.
What is computer information technology cyber?
Computer information technology cyber refers to the study and practice of protecting computer systems, networks, and data from cyber attacks.
Who is required to file computer information technology cyber?
Any organization or business that utilizes computer systems and networks is required to file computer information technology cyber.
How to fill out computer information technology cyber?
To fill out computer information technology cyber, one must provide detailed information about their organization's cyber security measures, potential risks, and incident response procedures.
What is the purpose of computer information technology cyber?
The purpose of computer information technology cyber is to ensure the security and integrity of computer systems, networks, and data.
What information must be reported on computer information technology cyber?
Information such as cyber security policies, incident response plans, risk assessments, and any past cyber attacks must be reported on computer information technology cyber.
Fill out your computer information technology cyber online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Computer Information Technology Cyber is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















