Form Application - Public Key Online Grátis
Drop document here to upload
Up to 100 MB for PDF and up to 25 MB for DOC, DOCX, RTF, PPT, PPTX, JPEG, PNG, JFIF, XLS, XLSX or TXT
Note: Integration described on this webpage may temporarily not be available.
0
Forms filled
0
Forms signed
0
Forms sent
Discover the simplicity of processing PDFs online
Upload your document in seconds
Fill out, edit, or eSign your PDF hassle-free

Download, export, or share your edited file instantly
Top-rated PDF software recognized for its ease of use, powerful features, and impeccable support






Every PDF tool you need to get documents done paper-free
Create & edit PDFs
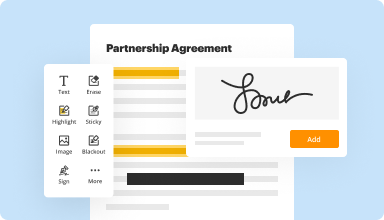
Generate new PDFs from scratch or transform existing documents into reusable templates. Type anywhere on a PDF, rewrite original PDF content, insert images or graphics, redact sensitive details, and highlight important information using an intuitive online editor.
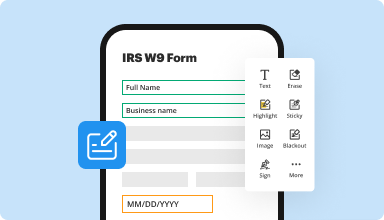
Fill out & sign PDF forms
Say goodbye to error-prone manual hassles. Complete any PDF document electronically – even while on the go. Pre-fill multiple PDFs simultaneously or extract responses from completed forms with ease.
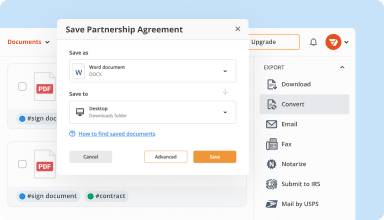
Organize & convert PDFs
Add, remove, or rearrange pages inside your PDFs in seconds. Create new documents by merging or splitting PDFs. Instantly convert edited files to various formats when you download or export them.
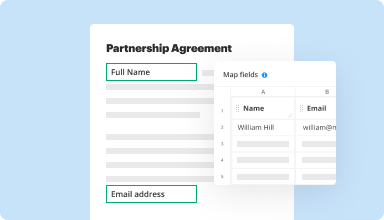
Collect data and approvals
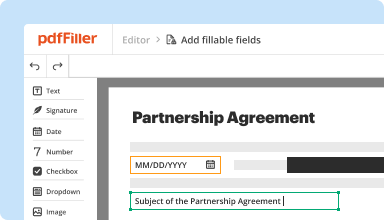
Transform static documents into interactive fillable forms by dragging and dropping various types of fillable fields on your PDFs. Publish these forms on websites or share them via a direct link to capture data, collect signatures, and request payments.
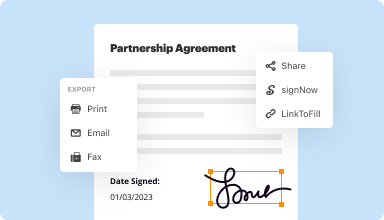
Export documents with ease
Share, email, print, fax, or download edited documents in just a few clicks. Quickly export and import documents from popular cloud storage services like Google Drive, Box, and Dropbox.
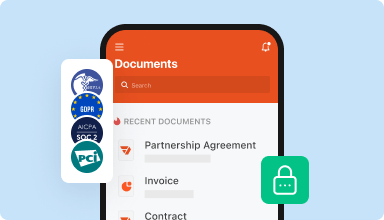
Store documents safely
Store an unlimited number of documents and templates securely in the cloud and access them from any location or device. Add an extra level of protection to documents by locking them with a password, placing them in encrypted folders, or requesting user authentication.
Customer trust by the numbers
64M+
users worldwide
4.6/5
average user rating
4M
PDFs edited per month
9 min
average to create and edit a PDF
Join 64+ million people using paperless workflows to drive productivity and cut costs
Why choose our PDF solution?
Cloud-native PDF editor
Access powerful PDF tools, as well as your documents and templates, from anywhere. No installation needed.
Top-rated for ease of use
Create, edit, and fill out PDF documents faster with an intuitive UI that only takes minutes to master.
Industry-leading customer service
Enjoy peace of mind with an award-winning customer support team always within reach.
What our customers say about pdfFiller
See for yourself by reading reviews on the most popular resources:
I am too Busy at the present time but I find the program very helpful. I would like to review the program after I get into it in the tax season for more comments.
2017-01-12
The outputs of the system are great ... just your opening page is a bit confusing. I just wanted to look convert a document but couldn't see conversion icons - finally worked out that I have to use Add New button - remember people are coming to your website from other portals they have used before - and like me they look for a document conversion tool!
2019-11-19
Makes creating and filling out forms a breeze!
Overall, if you need to have PDF forms in your life, you couldn't ask for a better solution than this. I'm just waiting for the day when it the basic version isn't free anymore--let's hope it never comes!
We live in the twenty-first century. So few things rankle me more than seeing someone's sent me a Word document and pretended it's a form. The same is true for people who send me PDFs and expect me to print and fill them out by hand. PDFfiller is the solution to all these problems and more. It makes the sending and receiving of forms so easy that even a kid could do it.
I really have no complaints about PDFfiller. It does what it needs to do quickly and easily, and it didn't take me long to learn how to use it. Even things that once seemed formidable to me (for instance, the dreaded splitting and combining of PDFs) is easy with PDFfiller.
2019-09-09
This is a very handy tool
This is a very handy tool, the only problem is the price, you could give a discount for students or something, otherwise a very lifesaving thing.
2024-06-14
I think you should ask me this again in…
I think you should ask me this again in another month. I'm very new to using this, and far from computer literate, but so far I am finding it very easy & extremely useful.
Thank you!
Lisa Marie
2021-11-23
What do you like best?
How easy it is to modify PDFs and being able to protect them
What do you dislike?
Not being able to upload more than five pages at a time
What problems are you solving with the product? What benefits have you realized?
I can upload and modify a document instead of starting it all over. I can fax my papers, and I will receive confirmation.
2021-10-14
A 1st Class Product - I Highly Recommend it !
I have been their client for many years , and I would recommend anyone to be come one , you have only to gain as their product is Fantastic .I must complement their customer support team , they are very much client oriented and they would resolve any issues that you might incur at no time.
2021-08-16
Best customer service ever
Best customer service ever! I accidentally signed for a year and it cost me an amount of money I can't afford (it doesn't seem much, but when your local currency is way behind USD, it greatly hurts your wallet). After reaching Rachel on pdfFiller's customer service team, they not only refunded me but also waived a month of free access. I couldn't be happier of using it! Recommending it to all my friends, from now on!
2021-05-13
Pets lives do matter too
the very easy way to register your family pet pets lives to do matter register your dog help me keep up with the history of the pets
2021-04-18
Form Application - Public Key Feature
The Form Application with Public Key feature simplifies and secures your online interactions. By leveraging public key technology, your data remains protected while enabling easy access and validation.
Key Features of Public Key
Secure data encryption and decryption
Identity verification for users
Seamless integration with existing systems
User-friendly interface for easy navigation
Scalable solutions to meet growing demands
Potential Use Cases
Securely transmitting sensitive information
Validating user identity for online services
Facilitating secure communications between parties
Enhancing e-commerce transactions with added security
Managing access control in corporate environments
With the Form Application's Public Key feature, you can address key security concerns. It helps protect your data from unauthorized access, ensuring that only intended users can obtain and use it. This simple and effective tool strengthens your online presence and builds trust with your users.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What if I have more questions?
Contact Support
What are the applications of public key cryptography?
Applications. The most obvious application of a public key encryption system is in encrypting communication to provide confidentiality a message that a sender encrypts using the recipient's public key can be decrypted only by the recipient's paired private key.
What is public key cryptography used for?
A Definition of Public Key Cryptography Public key cryptography uses a pair of keys to encrypt and decrypt data to protect it against unauthorized access or use. Network users receive a public and private key pair from certification authorities. This key is used to encrypt the message, and to send it to the recipient.
What is public key cryptography and why is it important?
Public key cryptography has become an important means of ensuring confidentiality, notably through its use of key distribution, where users seeking private communication exchange encryption keys. It also features digital signatures which allow users to sign keys to verify their identities.
Why is public key cryptography?
Public key cryptography uses a pair of keys to encrypt and decrypt data to protect it against unauthorized access or use. Network users receive a public and private key pair from certification authorities. If other users want to encrypt data, they get the intended recipient's public key from a public directory.
What is public key certificate and how does it work?
Public key certificates are part of a public key infrastructure that deals with digitally signed documents. The other components are public key encryption, trusted third parties (such as the certification authority), and mechanisms for certificate publication and issuing.
How many keys are there in public key cryptography and what are they used for?
For every user, there is 1 Private key and 1 Public key. The Private key is used to decrypt messages from other users. The Public key is used by everyone else to encrypt messages for that user. If you have 5 users, there are 5 Private keys and 5 Public keys.
What are the applications of cryptography?
Applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications. Cryptography prior to the modern age was effectively synonymous with encryption, the conversion of information from a readable state to apparent nonsense.
What is cryptography and its application?
Cryptography is used in many applications like banking transactions cards, computer passwords, and e- commerce transactions. Three types of cryptographic techniques used in general.
#1 usability according to G2
Try the PDF solution that respects your time.






