Protected Quantity Notification Grátis
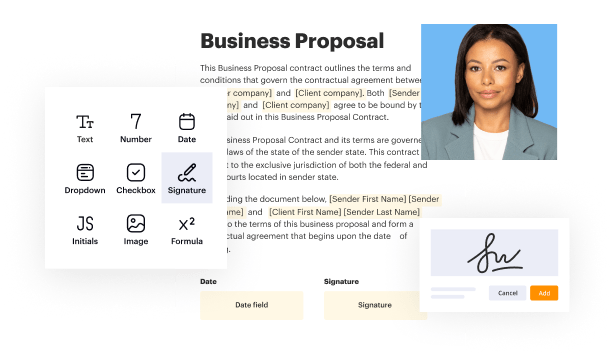
Create a legally-binding electronic signature and add it to contracts, agreements, PDF forms, and other documents – regardless of your location. Collect and track signatures with ease using any device.
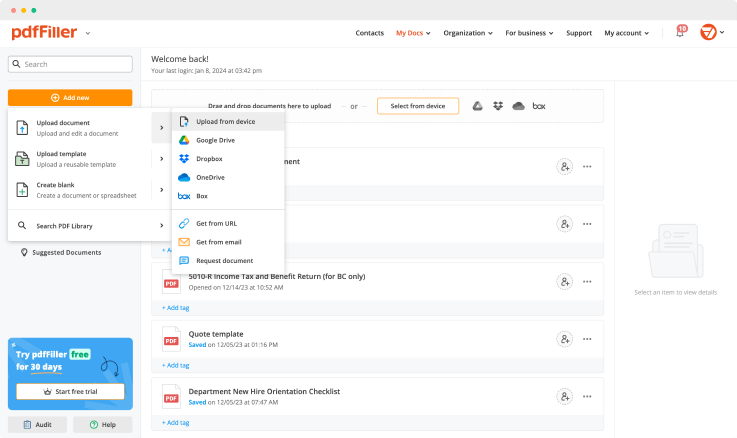
Drop document here to upload
Up to 100 MB for PDF and up to 25 MB for DOC, DOCX, RTF, PPT, PPTX, JPEG, PNG, JFIF, XLS, XLSX or TXT
Note: Integration described on this webpage may temporarily not be available.

Upload a document

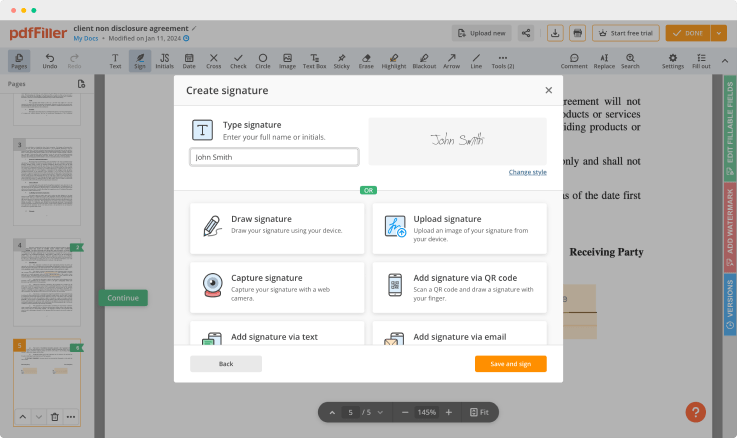
Generate your customized signature

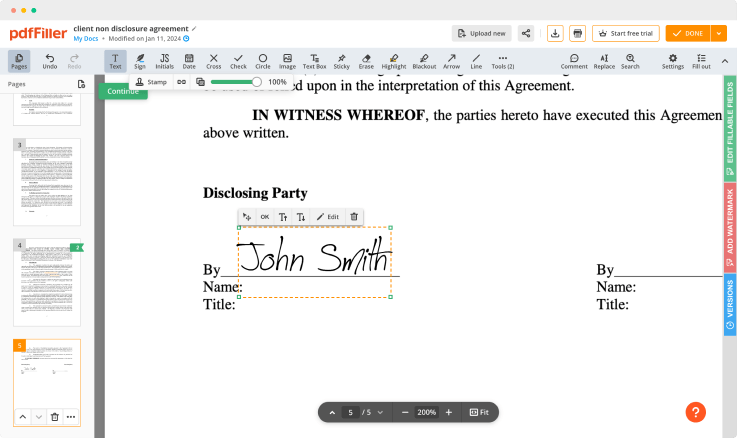
Adjust the size and placement of your signature

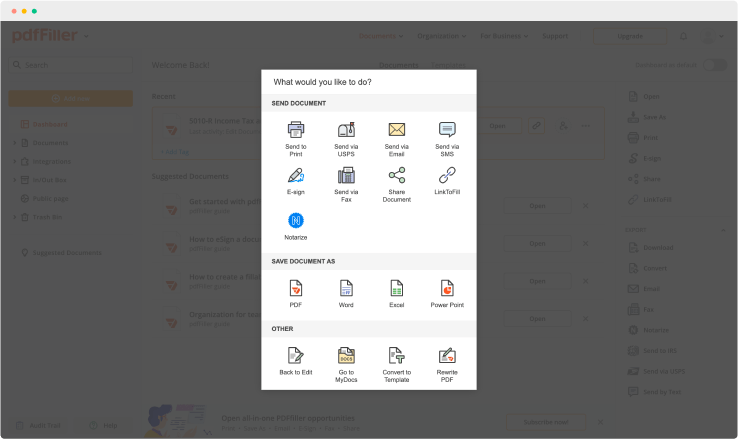
Download, share, print, or fax your signed document
Join the world’s largest companies
Employees at these companies use our products.
How to Add a Signature to PDF (and Send it Out for Signature)
Watch the video guide to learn more about pdfFiller's online Signature feature

pdfFiller scores top ratings in multiple categories on G2
4.6/5
— from 710 reviews








Why choose pdfFiller for eSignature and PDF editing?

Cross-platform solution
Upload your document to pdfFiller and open it in the editor.

Unlimited document storage
Generate and save your electronic signature using the method you find most convenient.

Widely recognized ease of use
Resize your signature and adjust its placement on a document.

Reusable templates & forms library
Save a signed, printable document on your device in the format you need or share it via email, a link, or SMS. You can also instantly export the document to the cloud.
The benefits of electronic signatures
Bid farewell to pens, printers, and paper forms.

Efficiency
Enjoy quick document signing and sending and reclaim hours spent on paperwork.

Accessibility
Sign documents from anywhere in the world. Speed up business transactions and close deals even while on the go.

Cost savings
Eliminate the need for paper, printing, scanning, and postage to significantly cut your operational costs.

Security
Protect your transactions with advanced encryption and audit trails. Electronic signatures ensure a higher level of security than traditional signatures.

Legality
Electronic signatures are legally recognized in most countries around the world, providing the same legal standing as a handwritten signature.

Sustainability
By eliminating the need for paper, electronic signatures contribute to environmental sustainability.
Enjoy straightforward eSignature workflows without compromising data security

GDPR compliance
Regulates the use and holding of personal data belonging to EU residents.

SOC 2 Type II Certified
Guarantees the security of your data & the privacy of your clients.

PCI DSS certification
Safeguards credit/debit card data for every monetary transaction a customer makes.

HIPAA compliance
Protects the private health information of your patients.

CCPA compliance
Enhances the protection of personal data and the privacy of California residents.
Protected Quantity Notification Feature
The Protected Quantity Notification feature helps you maintain control over your inventory levels. With this tool, you can set alerts that notify you when your stock reaches a specific threshold. This ensures that you never run out of essential items while minimizing excess inventory.
Key Features
Customizable notifications for low stock levels
Easy integration with your existing inventory system
Real-time updates sent via email or app notifications
User-friendly dashboard for monitoring stock levels
Historical data analysis to improve stock management
Potential Use Cases and Benefits
Retailers can avoid stockouts during peak seasons
Manufacturers can ensure raw materials are always available
E-commerce businesses can manage order fulfillment efficiently
Restaurants can maintain sufficient food supplies to meet demand
Hospitality businesses can keep essential items available for guests
This feature addresses a common problem: running out of stock at critical times. By receiving timely alerts, you can refill inventory before it runs low. This solution not only enhances your operational efficiency but also improves customer satisfaction as you are less likely to disappoint them with unavailable products.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What if I have more questions?
Contact Support
Who must be notified by law of a breach affecting 500 or more patients?
If a breach affects 500 or more individuals, covered entities must notify the Secretary without unreasonable delay and in no case later than 60 days following a breach. If, however, a breach affects fewer than 500 individuals, the covered entity may notify the Secretary of such breaches on an annual basis.
Who is notified when PHI is breached?
HHS requires three types of entities to be notified in the case of a PHI data breach: individual victims, media, and regulators. The covered entity must notify those affected by the breach of unsecured PHI within 60 days of discovery of the breach.
How do you know if a HIPAA is breached?
Determine the nature and extent of PHI involved. Determine who the unauthorized individual was who used the PHI. Determine if the PHI was actually acquired or viewed. Determine the extent to which the risk to the PHI has been mitigated.
Who is responsible for notifying affected individuals about a PHI security breach?
HHS requires three types of entities to be notified in the case of a PHI data breach: individual victims, media, and regulators. The covered entity must notify those affected by the breach of unsecured PHI within 60 days of discovery of the breach. That can be a question.
When a suspected breach of PHI has been confirmed a hospital must report the violation to?
Any breach of unsecured protected health information must be reported to the covered entity within 60 days of the discovery of a breach. While this is the absolute deadline, business associates must not delay notification unnecessarily.
How soon must a HIPAA breach be reported?
Data Breaches Experienced by HIPAA Business Associates Any breach of unsecured protected health information must be reported to the covered entity within 60 days of the discovery of a breach. While this is the absolute deadline, business associates must not delay notification unnecessarily.
Do HIPAA violations have to be reported?
HIPAA Breach Notification Rule. Not all HIPAA violations are required to be reported to the relevant patient or HHS. Under the breach notification rule, covered entities are only required to self-report if there is a breach of unsecured PHI.
What is the correct order of steps that must be taken if there is a breach of HIPAA information or data?
Stop the breach. Terminate improper access to PHI. Retrieve any PHI that was improperly disclosed. And obtain assurances from recipients that they have not used or disclosed the PHI, and/or will not, further use or disclose PHI that was improperly accessed. Document your actions and the recipient's response.
Ready to try pdfFiller's? Protected Quantity Notification Grátis
Upload a document and create your digital autograph now.