Furthermore, many online discussions and technical analyses fail to make clear distinctions between types of spyware. We define six classes of malware, categorize malware by type, and derive a mathematical model that predicts the likelihood of an infected computer possessing a certain type of spyware. By integrating an automated tool that collects the most widely used spyware tools and analyzes them for features that correlate with detection, we predict, as well as show that our model can correctly classify spyware collected by a single company. Author Summary. Most malware is benign, meaning it contains no harmful features. However, the proliferation of spyware, including malware that does not exist, is a concern for millions of Internet-connected computers worldwide. The focus of malware research is to provide information on the prevalence of malware. Although many studies have studied this issue, only a handful have attempted to classify malware by type. We use a mathematical tool called machine learning to derive a mathematical model that can correctly classify malware collected by a single company. Using our new classification system, we anticipate that we can improve the probability of being discovered when conducting network-analysis. Keywords: Malware, Computer, Malware Analysis, Automated Spyware Collection and Analysis, Computer Learning, Natural Language Processing Keywords: Computer, Computer Forensics, Natural Language Processing, Malware
1. Introduction 1.1 Cyber-criminals 1.2 The prevalence of malware 1.3 The effectiveness of malware detection 1.4 Predictions of threat to users 1.5 Summary The Internet is home to an enormous range of malware. According to a report by Symantec, approximately 80% of Internet traffic contains malicious code.2 However, many online discussions and technical analyses fail to make clear distinctions between types of spyware. For the most part, discussions use the term espionage and malware interchangeably. In particular, there is little differentiation of the types of malware. For example, it is common knowledge that spyware is spyware and therefore classified as spyware, therefore classified as malware. In reality, all malware is malicious. While the two terms are often used interchangeably, they have important differences. Whereas spies and spies work for intelligence agencies such as the CIA and FBI, criminals work for hackers. Hacking is the process of obtaining information from others, typically by stealth, in order to sell it or share it. To become a full-fledged hacker, one usually requires high-level knowledge (or skills) such as computer engineering, networking, and programming.

Get the free Automated Spyware Collection and Analysis - cs ucsb
Show details
Automated Spyware Collection and Analysis Andreas Stamminger1, Christopher Kruegel1, Giovanni Vigna1, and Engine Kirda2 1 University of California, Santa Barbara as, Chris, via cs.UCSB.edu 2 Institute
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
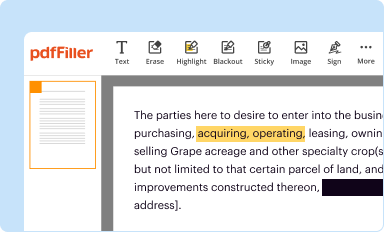
Edit your automated spyware collection and form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
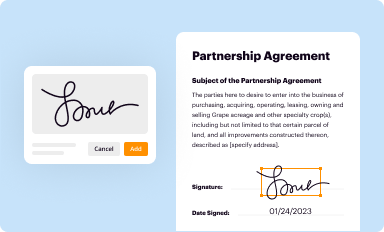
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
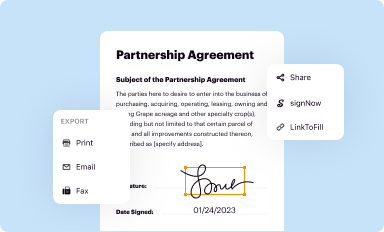
Share your form instantly
Email, fax, or share your automated spyware collection and form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing automated spyware collection and online
In order to make advantage of the professional PDF editor, follow these steps below:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit automated spyware collection and. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is automated spyware collection and?
Automated spyware collection is the process of gathering and collecting data on spyware instances automatically.
Who is required to file automated spyware collection and?
Entities involved in the development, distribution, or use of spyware are required to file automated spyware collection.
How to fill out automated spyware collection and?
To fill out automated spyware collection, you need to provide information about the spyware instances, such as their nature, purpose, and distribution methods.
What is the purpose of automated spyware collection and?
The purpose of automated spyware collection is to gather data on spyware instances for analysis and monitoring purposes in order to combat cyber threats.
What information must be reported on automated spyware collection and?
On automated spyware collection, you must report information about the spyware instances, including their technical characteristics, functionality, and potential risks.
When is the deadline to file automated spyware collection and in 2023?
The deadline to file automated spyware collection in 2023 is currently not available. Please refer to the official guidelines for the specific deadline.
What is the penalty for the late filing of automated spyware collection and?
The penalty for the late filing of automated spyware collection may vary depending on the jurisdiction and applicable regulations. Please consult the relevant authorities or legal experts for accurate information.
How can I send automated spyware collection and for eSignature?
Once your automated spyware collection and is complete, you can securely share it with recipients and gather eSignatures with pdfFiller in just a few clicks. You may transmit a PDF by email, text message, fax, USPS mail, or online notarization directly from your account. Make an account right now and give it a go.
How can I get automated spyware collection and?
It's simple with pdfFiller, a full online document management tool. Access our huge online form collection (over 25M fillable forms are accessible) and find the automated spyware collection and in seconds. Open it immediately and begin modifying it with powerful editing options.
How do I fill out the automated spyware collection and form on my smartphone?
Use the pdfFiller mobile app to fill out and sign automated spyware collection and. Visit our website (https://edit-pdf-ios-android.pdffiller.com/) to learn more about our mobile applications, their features, and how to get started.
Fill out your automated spyware collection and online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.





















