Denial of Service attacks target the ability of legitimate users to communicate with systems under their control, and therefore can significantly reduce a system's functionality. Denial of service attacks are discussed in this paper. A denial of service attack involves sending a large amount of traffic on many networks toward a target system (usually a server). This causes a large quantity of requests to be processed, slowing down the system while providing no assurance to the attacker to stop when the intended targets are notified and shut down the compromised system. The target system's ability to respond is reduced while simultaneously increasing the attacker's resources for future attacks. The ability of the target system to respond by reducing the attack can be further reduced by allowing the attacker to block access from the target system's end-users. To analyze a denial of service attack, we propose a novel analysis of the network traffic between two servers. We perform two types of traffic flows: one used to send and receive data between the two servers, and the second to process or modify the data sent between the two servers. A large-scale experiment shows our techniques will successfully block these two types of data flow. We prove that analysis of these flows (denial of service and data traffic analyzes) is equivalent to performing a Distributed Information Dependent (DID). A DIS enables a network administrator to perform a denial of service attack by denying or disrupting access to legitimate users and resources on the victim system. Denial of service attacks often are conducted by placing a server in a state which is not responding to requests which require authentication, typically when a new user's account is initialized. This usually causes the system to be locked down, preventing legitimate use of the system. Since these attacks can be carried out by remote attackers without user interaction, it is important that the user or system administrator be allowed to verify each request. This is generally done using a Distributed Denial-of-Service (DDoS) Attack (e.g., by sending many requests to a single server). In many cases, a DDoS attack is carried out by a centralized third party (web hosting provider, internet service provider [ISP], hosting server, web host [WHM]). In order to conduct a DDoS attack, the third party acts like a Denial of service attacker (Figure 1), sending packets to the victim system on a daily basis with requests requesting access to certain resources (data, system resources, etc.) of the targeted system.

Get the free Intrusion ripple analysis in distributed information systems - DoI
Show details
Intrusion Ripple Analysis in Distributed Information Systems Stephen S. You and Jun Zhu Computer Science and Engineering Department Arizona State University Tempe, AZ 85287, U.S.A. Email: you ASU.edu
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
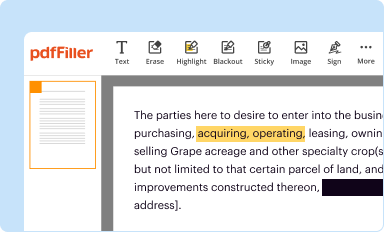
Edit your intrusion ripple analysis in form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your intrusion ripple analysis in form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit intrusion ripple analysis in online
To use the professional PDF editor, follow these steps below:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit intrusion ripple analysis in. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Register for an account and see for yourself!
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is intrusion ripple analysis in?
Intrusion ripple analysis is a method used to assess the potential impact and consequences of an intrusion or security breach on a system or network.
Who is required to file intrusion ripple analysis in?
The responsibility of filing intrusion ripple analysis typically falls on the organization or entity that owns or operates the system or network that is being assessed.
How to fill out intrusion ripple analysis in?
To fill out intrusion ripple analysis, you would typically need to gather relevant information about the system or network, identify potential vulnerabilities, assess potential consequences of an intrusion, and propose mitigation measures.
What is the purpose of intrusion ripple analysis in?
The purpose of intrusion ripple analysis is to identify and assess the potential impact and consequences of an intrusion or security breach, in order to make informed decisions about security measures and mitigation strategies.
What information must be reported on intrusion ripple analysis in?
The specific information required for intrusion ripple analysis may vary depending on the system or network being assessed, but typically it would include information about vulnerability assessments, potential attack vectors, potential consequences, and proposed mitigation measures.
When is the deadline to file intrusion ripple analysis in in 2023?
The deadline to file intrusion ripple analysis in 2023 would depend on the specific regulations or requirements set by relevant authorities or industry standards. To determine the exact deadline, you should refer to the applicable guidelines or consult with the appropriate regulatory body.
What is the penalty for the late filing of intrusion ripple analysis in?
The penalties for late filing of intrusion ripple analysis may vary depending on the specific regulations, authorities, and applicable laws. To understand the potential penalties, you should consult the relevant regulations or seek legal advice.
How can I manage my intrusion ripple analysis in directly from Gmail?
It's easy to use pdfFiller's Gmail add-on to make and edit your intrusion ripple analysis in and any other documents you get right in your email. You can also eSign them. Take a look at the Google Workspace Marketplace and get pdfFiller for Gmail. Get rid of the time-consuming steps and easily manage your documents and eSignatures with the help of an app.
Can I create an electronic signature for signing my intrusion ripple analysis in in Gmail?
It's easy to make your eSignature with pdfFiller, and then you can sign your intrusion ripple analysis in right from your Gmail inbox with the help of pdfFiller's add-on for Gmail. This is a very important point: You must sign up for an account so that you can save your signatures and signed documents.
How can I edit intrusion ripple analysis in on a smartphone?
The pdfFiller apps for iOS and Android smartphones are available in the Apple Store and Google Play Store. You may also get the program at https://edit-pdf-ios-android.pdffiller.com/. Open the web app, sign in, and start editing intrusion ripple analysis in.
Fill out your intrusion ripple analysis in online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.