Get the free Hacking Serverless Runtimes
Show details
Hacking Serverless Runtimes Profiling Lambda, Azure, and more. All updates to this Slide Deck will post on https://threatresponse.cloudPresenters : Who are they? Andrew Drug : andrewkrug Security
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
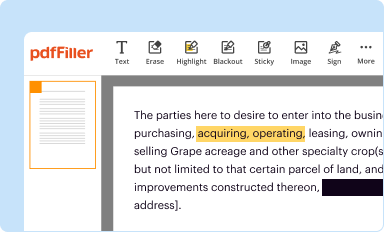
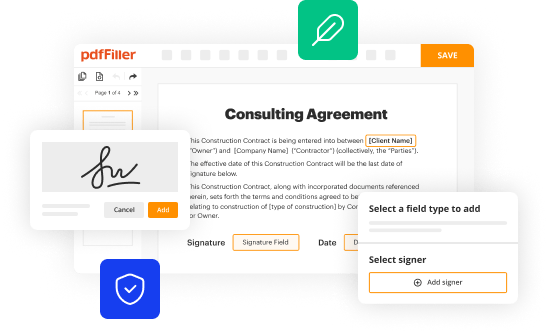
Edit your hacking serverless runtimes form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
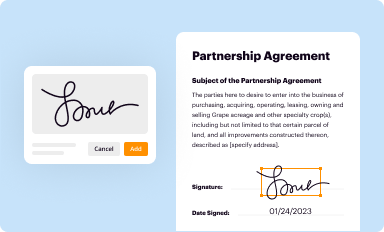
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
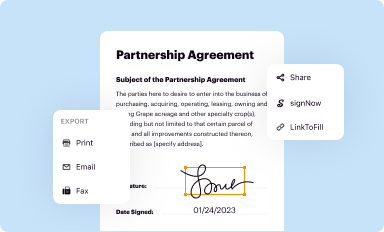
Share your form instantly
Email, fax, or share your hacking serverless runtimes form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing hacking serverless runtimes online
In order to make advantage of the professional PDF editor, follow these steps:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit hacking serverless runtimes. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
How to fill out hacking serverless runtimes
How to fill out hacking serverless runtimes
01
Step 1: Understand the basics of serverless runtimes and how they work.
02
Step 2: Identify the vulnerabilities and weaknesses in the serverless runtimes used.
03
Step 3: Gain access to the serverless runtime environment either through legitimate means or by exploiting the identified vulnerabilities.
04
Step 4: Analyze the runtime environment to determine potential entry points for hacking.
05
Step 5: Execute specific hacking techniques and scripts to compromise the serverless runtimes.
06
Step 6: Continually monitor and evaluate the compromised runtimes to maintain persistent control and gather sensitive information.
07
Step 7: Cover tracks and erase any evidence of hacking activities to prevent detection.
08
Step 8: Stay updated with the latest hacking techniques and vulnerabilities in serverless runtimes to continuously exploit them.
Who needs hacking serverless runtimes?
01
Cybercriminals or hackers who wish to exploit vulnerabilities in serverless runtimes for personal gain.
02
Penetration testers or security researchers who want to assess the security of serverless applications and identify potential weaknesses.
03
Security professionals who need to understand the various attack vectors and defense mechanisms associated with serverless runtimes.
04
Developers or system administrators who want to enhance the security of their serverless applications by identifying and mitigating potential vulnerabilities.
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send hacking serverless runtimes to be eSigned by others?
hacking serverless runtimes is ready when you're ready to send it out. With pdfFiller, you can send it out securely and get signatures in just a few clicks. PDFs can be sent to you by email, text message, fax, USPS mail, or notarized on your account. You can do this right from your account. Become a member right now and try it out for yourself!
How do I edit hacking serverless runtimes straight from my smartphone?
The easiest way to edit documents on a mobile device is using pdfFiller’s mobile-native apps for iOS and Android. You can download those from the Apple Store and Google Play, respectively. You can learn more about the apps here. Install and log in to the application to start editing hacking serverless runtimes.
How do I fill out hacking serverless runtimes on an Android device?
Use the pdfFiller app for Android to finish your hacking serverless runtimes. The application lets you do all the things you need to do with documents, like add, edit, and remove text, sign, annotate, and more. There is nothing else you need except your smartphone and an internet connection to do this.
Fill out your hacking serverless runtimes online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.