Get the free Common Vulnerabilities and Exposures Search ... - PINGPDF.COM
Show details
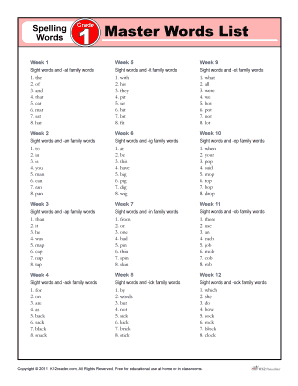
Info()Page 1 of 19PHP Version 5.6.30SystemFreeBSD s41.server. Hotpoint.ch 10.3RELEASEp3 FreeBSD 10.3RELEASEp3 #12 r300097M: Wed May 18 00:39:17 UTC 2016 root port10. Adm.Hotpoint.ch:/USR/obj/USR/src/says/HOTPOINT
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
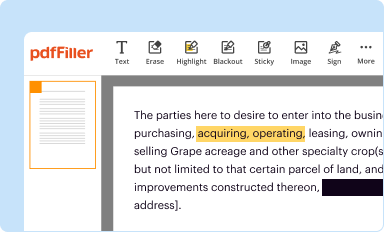
Edit your common vulnerabilities and exposures form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
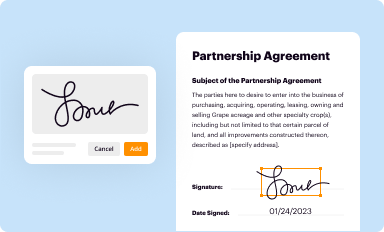
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your common vulnerabilities and exposures form via URL. You can also download, print, or export forms to your preferred cloud storage service.
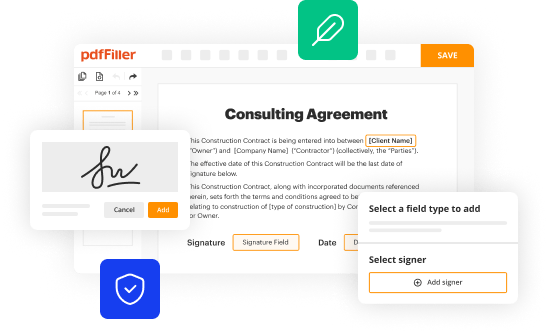
Editing common vulnerabilities and exposures online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit common vulnerabilities and exposures. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
How to fill out common vulnerabilities and exposures
How to fill out common vulnerabilities and exposures
01
To fill out common vulnerabilities and exposures, follow these steps:
02
Start by identifying potential vulnerabilities in your system or software.
03
Make a list of these vulnerabilities and prioritize them based on their severity.
04
Research existing common vulnerabilities and exposures (CVE) in the CVE database.
05
Compare the identified vulnerabilities with the existing CVEs to see if any match.
06
If a match is found, note down the CVE ID for that vulnerability.
07
For each identified vulnerability without a matching CVE, create a detailed description along with any relevant information.
08
Assign a unique CVE ID to each new vulnerability that does not have a matching CVE.
09
Document the steps to reproduce the vulnerability, the impact it may have, and any recommended mitigation or solution.
10
Optionally, notify the relevant stakeholders or security authorities about the identified vulnerabilities and their corresponding CVEs.
11
Regularly update and maintain your list of common vulnerabilities and exposures as new vulnerabilities emerge or existing ones are resolved.
Who needs common vulnerabilities and exposures?
01
Common vulnerabilities and exposures are needed by various parties, including:
02
- Software developers or vendors who want to track and document known vulnerabilities in their products.
03
- System or network administrators who need to assess and address vulnerabilities in their infrastructure.
04
- Security researchers who want to contribute to the identification and mitigation of vulnerabilities in software or systems.
05
- Organizations or individuals who are responsible for compliance and need to ensure they address all known vulnerabilities.
06
- Security professionals who want to stay informed about the latest vulnerabilities and the corresponding CVEs.
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I sign the common vulnerabilities and exposures electronically in Chrome?
Yes. You can use pdfFiller to sign documents and use all of the features of the PDF editor in one place if you add this solution to Chrome. In order to use the extension, you can draw or write an electronic signature. You can also upload a picture of your handwritten signature. There is no need to worry about how long it takes to sign your common vulnerabilities and exposures.
Can I edit common vulnerabilities and exposures on an iOS device?
You can. Using the pdfFiller iOS app, you can edit, distribute, and sign common vulnerabilities and exposures. Install it in seconds at the Apple Store. The app is free, but you must register to buy a subscription or start a free trial.
How do I complete common vulnerabilities and exposures on an Android device?
On Android, use the pdfFiller mobile app to finish your common vulnerabilities and exposures. Adding, editing, deleting text, signing, annotating, and more are all available with the app. All you need is a smartphone and internet.
Fill out your common vulnerabilities and exposures online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.