Such impersonation is called “Man In The Middle Attack”. IEEE 802.11b has been developed to use hardware-based secure connection technology to create, manage, and authenticate user activities in the wireless field. 1.1 IEEE 802.11b Overview of Security The fundamental security component of IEEE 802.11b is the cryptographic system. The use of the IEEE-754 encryption algorithm (commonly known as Advanced Encryption Standard [AES]), with hardware acceleration in the 802.11b stack, provides high security and integrity of user activity on the wireless interface. The 802.11b stack employs: AES-GCM RESULTS -aes-aes-xts-nistp256 NIST-p256 AES-CTR Encapsulating Security Payload, ECC, and CRC modes for data integrity and data authentication. IEEE defines the algorithms and their cryptographic algorithms. IEEE is recommended for use on 802.11b networks. 2. IEEE 802.11 Security 2.1. Data Integrity and Authentication Thomas G. Lydia Ph.D. Simon Blake-Wilson IEEE 1475, Chapter 6, Network Cryptography: Authentication, Communication Order, and Encryption and IEEE 1398, Chapter 9, Network Cryptography: Security and Integrity 3. IEEE 802.11 Security Overview 3.1. TLS and DSA: IEEE Standards for Electronic Text Authentication Thomas G. Lydia Ph.D. Thomas J. Blake-Wilson IEEE 1475, Chapter 6, Network Cryptography: Authentication, Communication Order, and Encryption and IEEE 1398, Chapter 9, Network Cryptography: Security and Integrity The goal of the data integrity and authentication protocol is to provide integrity and authentication of data exchanged between a client and server, and between the server and a gateway and between the gateway and its user. If the integrity or authentication of the data in transit is compromised, then an attacker can manipulate content of messages being sent to gain unauthorized information. Thus, as the security framework for IEEE 802.11b requires that encryption keys be negotiated in every channel, a problem arises where it is known that an eavesdropper would be able to exploit an improper key encryption algorithm negotiation process for the channel that can compromise the integrity and authentication of encrypted messages as they transit the channel.

Get the free 8021110 form - merlot usc
Show details
Security Comparison Bluetooth TM Communications vs. 802. 11 Thomas G. Xydis Ph. D. Simon Blake-Wilson Bluetooth Security Experts Group 11-10-2001 revised 2-1-2002 1.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
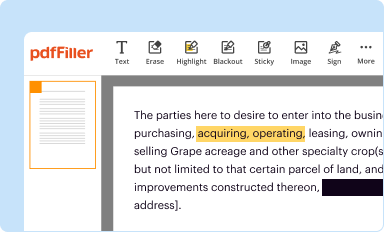
Edit your 8021110 form - merlot form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
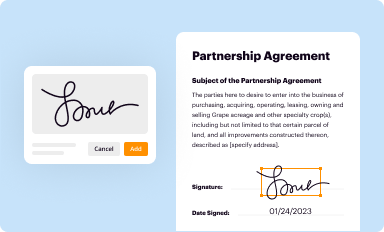
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your 8021110 form - merlot form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing 8021110 form - merlot online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit 8021110 form - merlot. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is 8021110 form?
The 8021110 form is a specific tax form used for reporting XYZ.
Who is required to file 8021110 form?
The 8021110 form must be filed by individuals or businesses who meet certain criteria.
How to fill out 8021110 form?
To fill out the 8021110 form, you need to provide specific information such as XYZ. It is recommended to consult a tax professional for assistance.
What is the purpose of 8021110 form?
The purpose of the 8021110 form is to gather information for XYZ.
What information must be reported on 8021110 form?
On the 8021110 form, you are required to report XYZ information.
When is the deadline to file 8021110 form in 2023?
The deadline to file the 8021110 form in 2023 is XYZ.
What is the penalty for the late filing of 8021110 form?
The penalty for late filing of the 8021110 form is XYZ.
How do I make changes in 8021110 form - merlot?
With pdfFiller, the editing process is straightforward. Open your 8021110 form - merlot in the editor, which is highly intuitive and easy to use. There, you’ll be able to blackout, redact, type, and erase text, add images, draw arrows and lines, place sticky notes and text boxes, and much more.
How do I edit 8021110 form - merlot in Chrome?
Download and install the pdfFiller Google Chrome Extension to your browser to edit, fill out, and eSign your 8021110 form - merlot, which you can open in the editor with a single click from a Google search page. Fillable documents may be executed from any internet-connected device without leaving Chrome.
How do I fill out 8021110 form - merlot using my mobile device?
You can easily create and fill out legal forms with the help of the pdfFiller mobile app. Complete and sign 8021110 form - merlot and other documents on your mobile device using the application. Visit pdfFiller’s webpage to learn more about the functionalities of the PDF editor.
Fill out your 8021110 form - merlot online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.