Get the free Guideline: Tokenization Product Security Guidelines
Show details
Guideline: Colonization Product Security Guidelines Version:1.0Date:April 2015Author:PCI Security Standards CouncilTokenization Product Security Guidelines Irreversible and Reversible TokensInformation
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
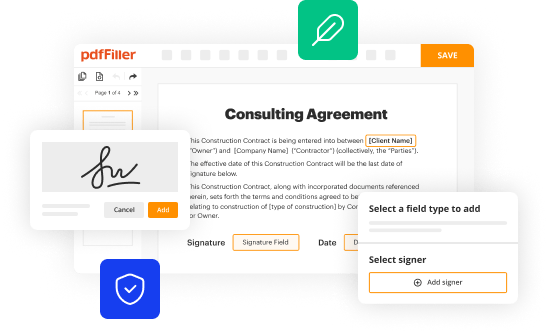
Edit your guideline tokenization product security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your guideline tokenization product security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit guideline tokenization product security online
Follow the guidelines below to benefit from a competent PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit guideline tokenization product security. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
It's easier to work with documents with pdfFiller than you could have believed. You may try it out for yourself by signing up for an account.
How to fill out guideline tokenization product security
How to fill out guideline tokenization product security?
01
Familiarize yourself with the purpose and objectives of the guideline tokenization product security. Understand the importance of protecting sensitive data and the role tokenization plays in achieving this.
02
Gather information about the specific tokenization product being used. This may include the name and version of the product, any additional modules or features, and any specific guidelines or documentation provided by the product vendor.
03
Understand the context and scope of the guideline tokenization product security. Determine which systems or applications will be impacted by the implementation of tokenization and the potential risks associated with data breaches.
04
Identify the key stakeholders involved in the implementation and maintenance of the tokenization product security. This may include IT security teams, data protection officers, system administrators, and application developers.
05
Evaluate the existing security measures in place and assess how tokenization can enhance or replace these measures. This may involve understanding current encryption methods, data masking techniques, and access controls.
06
Define the tokenization strategy based on your specific requirements and objectives. Consider factors such as which data elements need to be tokenized, the level of tokenization required (partial or complete), and any additional data protection mechanisms to be implemented alongside tokenization.
07
Develop a step-by-step implementation plan for the guideline tokenization product security. This should cover activities such as configuring the tokenization product, integrating it with existing systems, performing testing and validation, and training the relevant stakeholders.
08
Document the guidelines and procedures for using the tokenization product. Include instructions on how to generate and manage tokens, how to handle and store sensitive data, and any specific security controls or safeguards to be followed.
09
Continuously monitor and assess the effectiveness of the guideline tokenization product security. Regularly review logs and reports generated by the tokenization product, conduct vulnerability scans and penetration tests, and stay updated with any security patches or updates released by the vendor.
Who needs guideline tokenization product security?
01
Organizations that handle sensitive or confidential data, such as financial institutions, healthcare providers, and e-commerce companies, can benefit from implementing guideline tokenization product security. By tokenizing sensitive data, these organizations can reduce the risk of data breaches and protect the privacy of their customers.
02
IT security teams and data protection officers within these organizations play a crucial role in implementing and maintaining guideline tokenization product security. They are responsible for ensuring that the tokenization product is properly configured, integrated, and monitored to effectively protect sensitive data.
03
System administrators and application developers need guidance on how to incorporate the tokenization product into their existing systems and applications. They need to understand the guidelines and procedures for generating and managing tokens, as well as any additional security controls or safeguards that need to be implemented.
04
Compliance and regulatory bodies may require organizations to implement guideline tokenization product security as part of their data protection and privacy frameworks. Therefore, compliance officers and legal teams also need to have a clear understanding of the guidelines and procedures related to tokenization.
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is guideline tokenization product security?
Guideline tokenization product security is a set of security measures and protocols designed to protect tokenized data and prevent unauthorized access or fraud.
Who is required to file guideline tokenization product security?
Any organization that processes or stores tokenized data is required to file guideline tokenization product security.
How to fill out guideline tokenization product security?
Guideline tokenization product security can be filled out by providing detailed information about the security measures in place to protect tokenized data.
What is the purpose of guideline tokenization product security?
The purpose of guideline tokenization product security is to ensure the security and integrity of tokenized data and prevent data breaches or fraudulent activities.
What information must be reported on guideline tokenization product security?
Information that must be reported on guideline tokenization product security includes the security protocols, encryption methods, access controls, and monitoring tools used to protect tokenized data.
When is the deadline to file guideline tokenization product security in 2023?
The deadline to file guideline tokenization product security in 2023 is December 31st.
What is the penalty for the late filing of guideline tokenization product security?
The penalty for the late filing of guideline tokenization product security may include fines, sanctions, or other regulatory actions.
How do I make changes in guideline tokenization product security?
The editing procedure is simple with pdfFiller. Open your guideline tokenization product security in the editor. You may also add photos, draw arrows and lines, insert sticky notes and text boxes, and more.
How do I make edits in guideline tokenization product security without leaving Chrome?
Install the pdfFiller Google Chrome Extension in your web browser to begin editing guideline tokenization product security and other documents right from a Google search page. When you examine your documents in Chrome, you may make changes to them. With pdfFiller, you can create fillable documents and update existing PDFs from any internet-connected device.
How do I complete guideline tokenization product security on an Android device?
Complete guideline tokenization product security and other documents on your Android device with the pdfFiller app. The software allows you to modify information, eSign, annotate, and share files. You may view your papers from anywhere with an internet connection.
Fill out your guideline tokenization product security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.