Authenticate Sign Request For Free
Note: Integration described on this webpage may temporarily not be available.
0
Forms filled
0
Forms signed
0
Forms sent
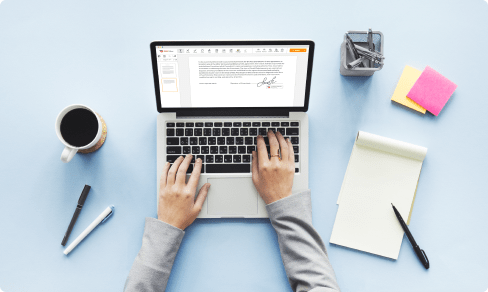
Upload your document to the PDF editor
Type anywhere or sign your form

Print, email, fax, or export

Try it right now! Edit pdf
Users trust to manage documents on pdfFiller platform
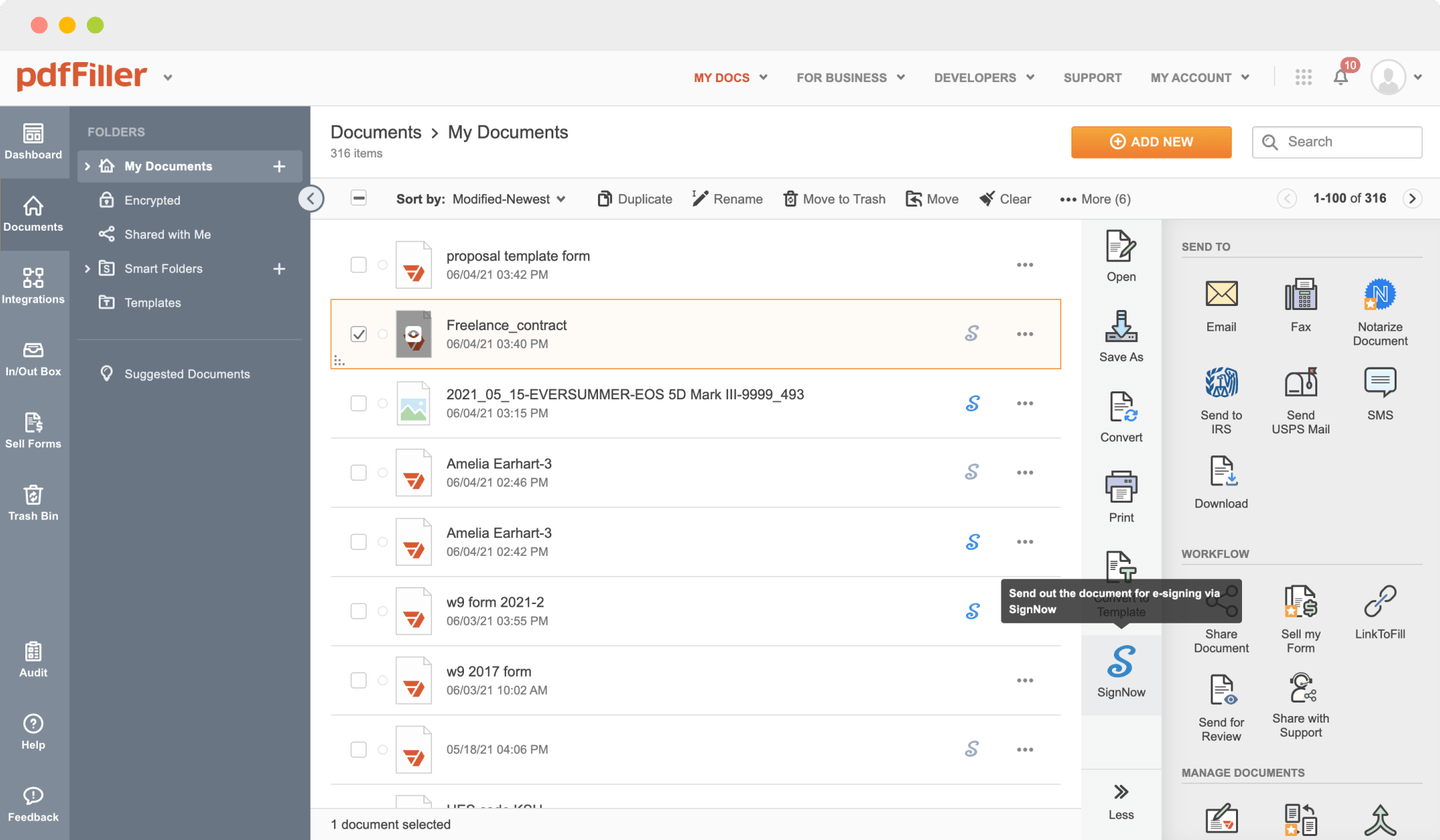
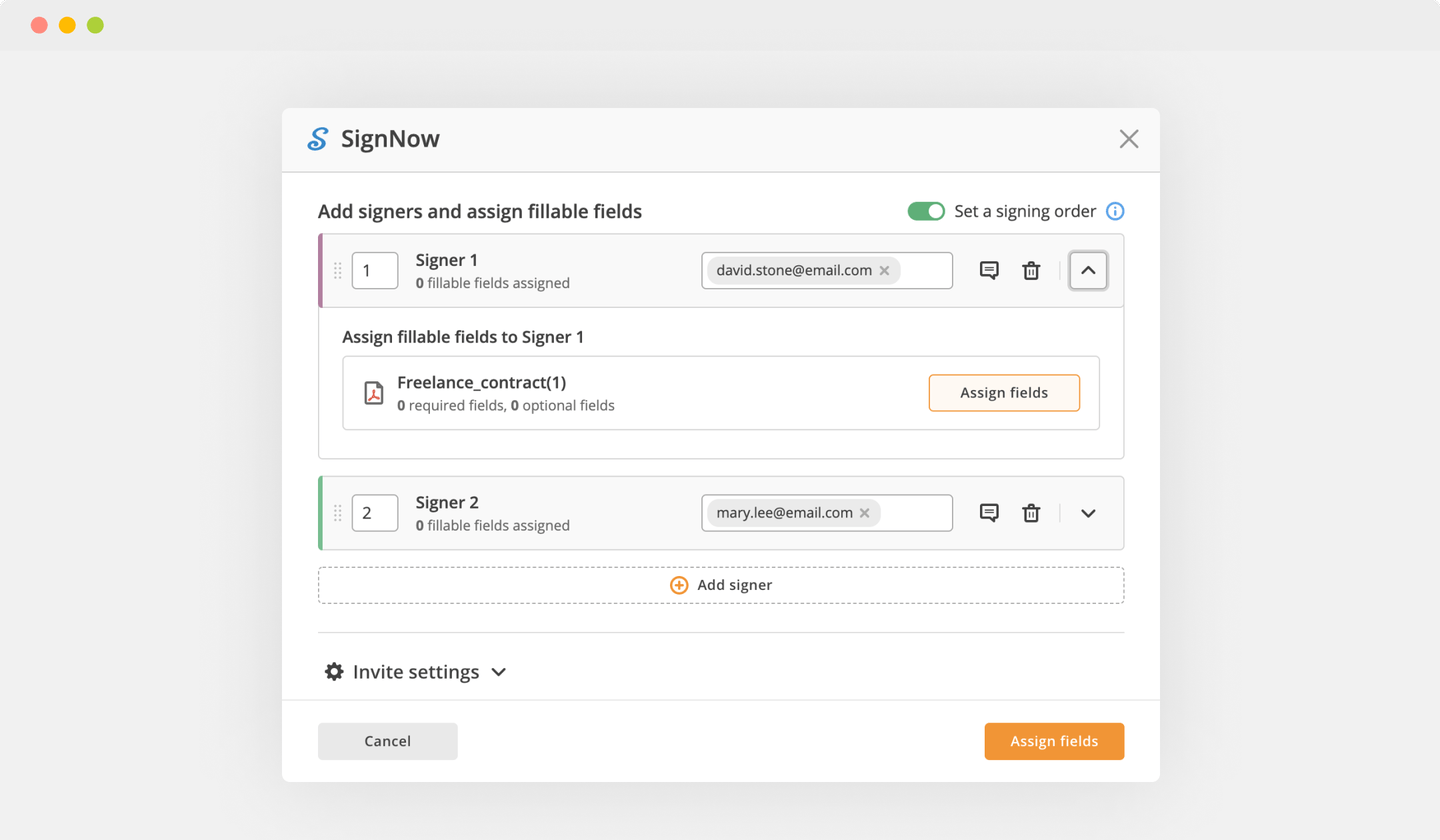
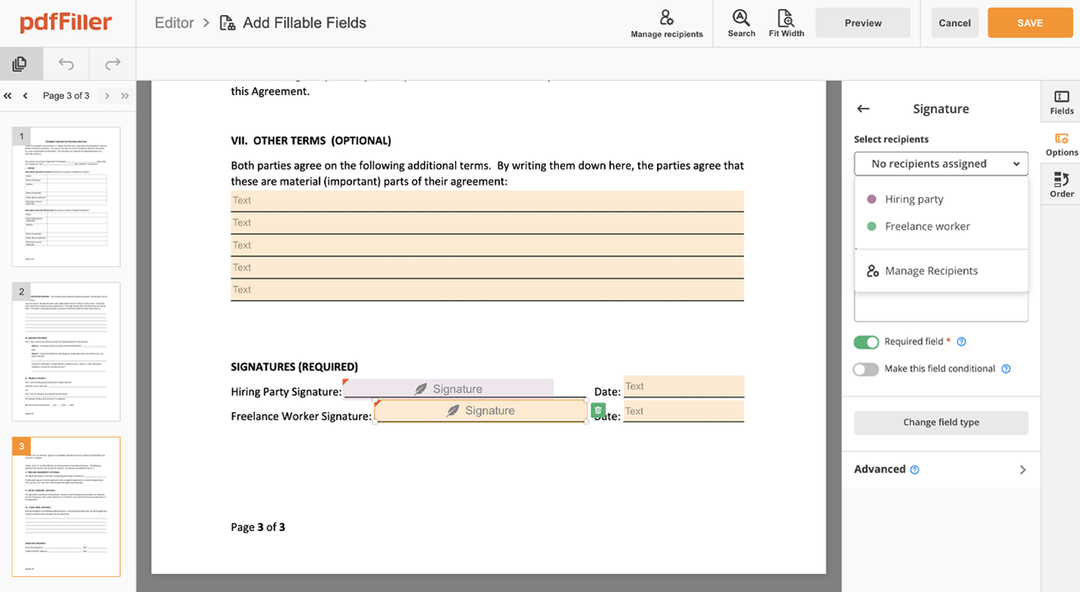
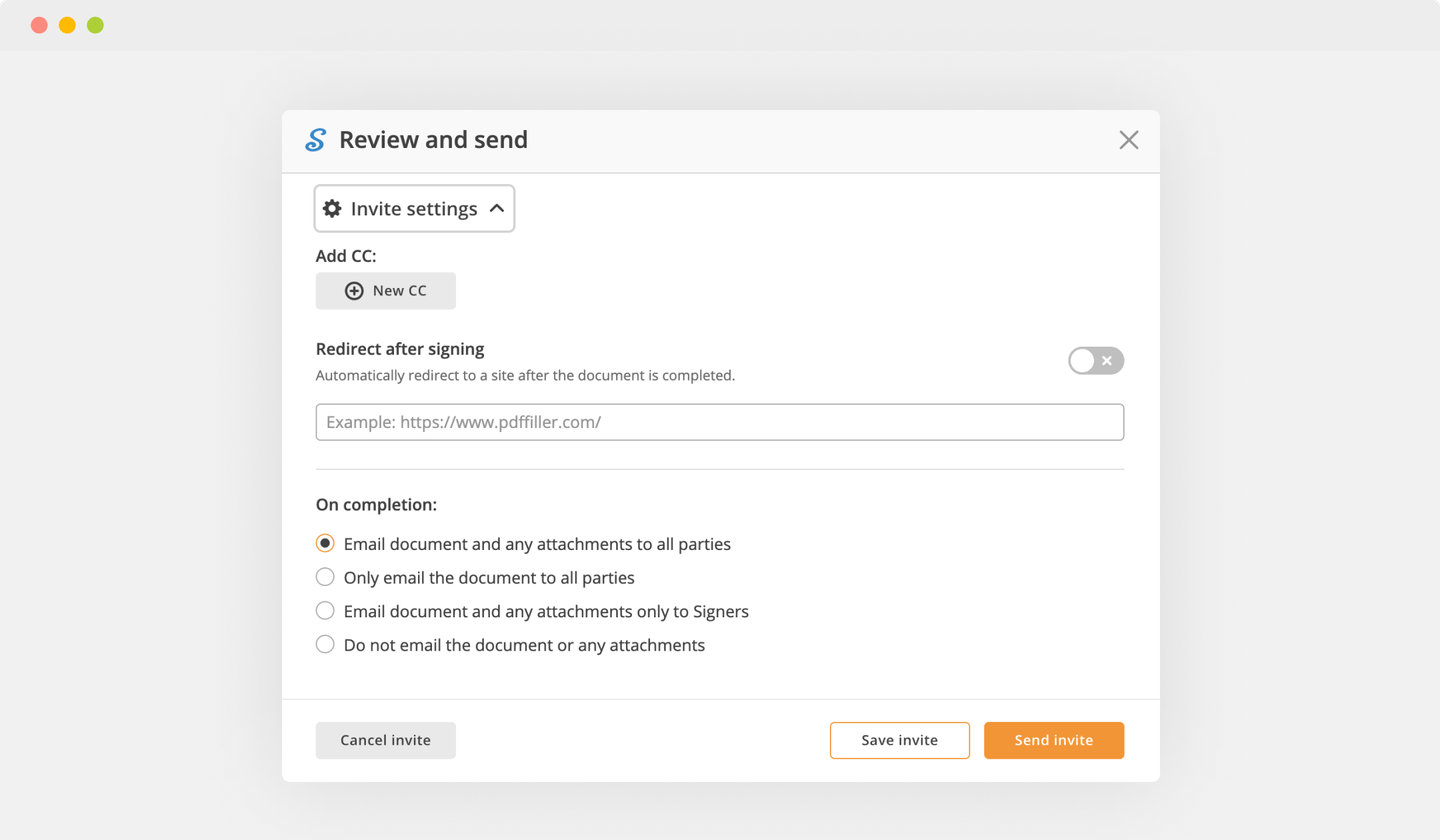
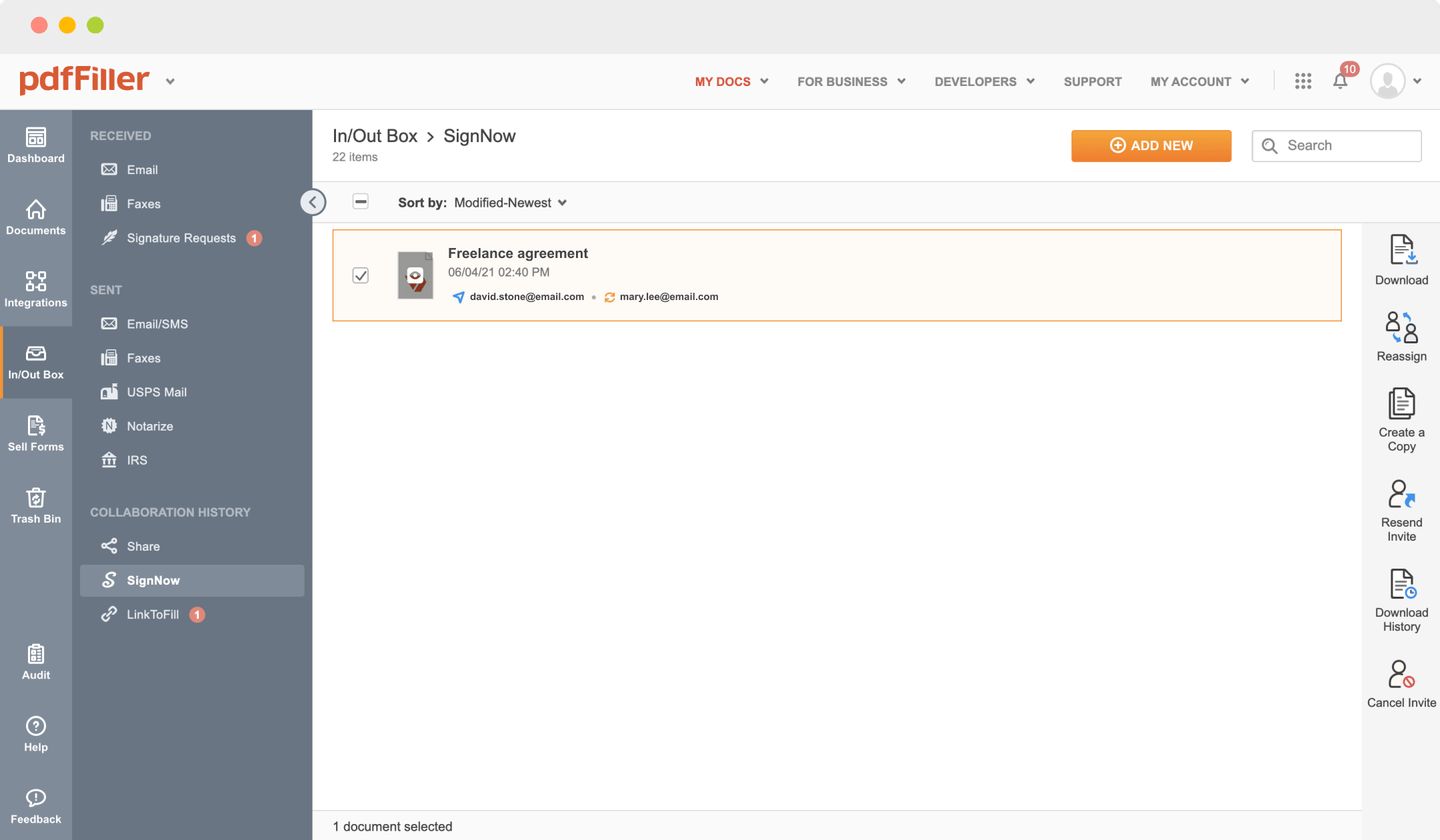
Send documents for eSignature with signNow
Create role-based eSignature workflows without leaving your pdfFiller account — no need to install additional software. Edit your PDF and collect legally-binding signatures anytime and anywhere with signNow’s fully-integrated eSignature solution.
All-in-one PDF software
A single pill for all your PDF headaches. Edit, fill out, eSign, and share – on any device.
pdfFiller scores top ratings in multiple categories on G2
How to Authenticate Sign Request
Stuck with multiple applications for managing documents? We have the perfect all-in-one solution for you. Use our tool to make the process efficient. Create document templates on your own, modify existing forms and more features, within your browser. Plus, you can Authenticate Sign Request and add major features like orders signing, reminders, requests, easier than ever. Pay as for a basic app, get the features as of a pro document management tools.
How-to Guide
How to edit a PDF document using the pdfFiller editor:
01
Upload your form to the uploading pane on the top of the page
02
Choose the Authenticate Sign Request feature in the editor's menu
03
Make the necessary edits to the document
04
Click the orange “Done" button at the top right corner
05
Rename your template if it's necessary
06
Print, share or download the template to your device
Video Review on How to Authenticate Sign Request
What our customers say about pdfFiller
See for yourself by reading reviews on the most popular resources:
LORI O
2014-05-14
AWESOME ALTHOUGH I THOUGHT I WAS GETTING A FREE TRIAL BUT NOTICED I WAS CHARGED $83.88 ON 5/6/14. DISAPPOINTING BUT IF I HAVE IT FOR A YEAR? I'M OKAY BUT YOU SHOULD BE AWARE. THIS COULD BE A PROBLEM IN THE FUTURE IF IT HASN'T ALREADY. BAD BUSINESS.

Olivia D.
2018-01-15
Best prices
This app save my tim. It is the cheapest option of all.
Pdfiller is very suitable. It is good for filling, sending, signing. Good support and reliable system.
Sometimes after the updates, it stops working as usual. Some time is needed for waiting for patches.


Get a powerful PDF editor for your Mac or Windows PC
Install the desktop app to quickly edit PDFs, create fillable forms, and securely store your documents in the cloud.

Edit and manage PDFs from anywhere using your iOS or Android device
Install our mobile app and edit PDFs using an award-winning toolkit wherever you go.

Get a PDF editor in your Google Chrome browser
Install the pdfFiller extension for Google Chrome to fill out and edit PDFs straight from search results.
List of extra features
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I sign AWS requests?
Task 1: Create a Canonical Request for Signature Version 4.
Task 2: Create a String to Sign for Signature Version 4.
Task 3: Calculate the Signature for AWS Signature Version 4.
Task 4: Add the Signature to the HTTP Request.
What is request signature in Amazon API?
The input includes the text of your request and your secret access key. The hash function returns a hash value that you include in the request as your signature. The signature is part of the Authorization header of your request. Amazon API Gateway supports authentication using AWS Signature Version 4.
How do I get AWS Secret Access Key?
To create a new secret access key for your root account, use the security credentials page. Expand the Access Keys section, and then click Create New Root Key.
To create a new secret access key for an IAM user, open the IAM console.
What is aws4?
aws4. A small utility to sign vanilla Node. Js http(s) request options using Amazon's AWS Signature Version 4. It also provides defaults for a number of core AWS headers and request parameters, making it very easy to query AWS services, or build out a fully-featured AWS library.
What is a canonical request?
Overview. A canonical request is a string that represents a specific HTTP request to Cloud Storage. You use a canonical request along with a cryptographic key, such as an RSA key, to create a signature that is then included in the actual request as authentication.
How do I authenticate AWS?
To authenticate from the console as a root user, you must sign in with your email address and password. As an IAM user, provide your account ID or alias, and then your username and password. To authenticate from the API or AWS CLI, you must provide your access key and secret key.
What is AWS authentication?
AWS Multi-Factor Authentication (MFA) is a simple best practice that adds an extra layer of protection on top of your username and password. You can enable MFA for your AWS account and for individual IAM users you have created under your account. MFA can be also be used to control access to AWS service APIs.
What is authentication in AWS?
AWS Multi-Factor Authentication (MFA) is a simple best practice that adds an extra layer of protection on top of your username and password. You can enable MFA for your AWS account and for individual IAM users you have created under your account. MFA can be also be used to control access to AWS service APIs.
What is IAM username AWS?
AWS Identity and Access Management (IAM) enables you to manage access to AWS services and resources securely. Using IAM, you can create and manage AWS users and groups, and use permissions to allow and deny their access to AWS resources.
How do you authenticate with tokens with Cognito?
Suggested clip
How to authenticate users with Tokens using Cognate - YouTubeYouTubeStart of suggested clipEnd of suggested clip
How to authenticate users with Tokens using Cognate - YouTube
Does Cognito use OAuth?
In addition to using the Amazon Cognito-specific user APIs to authenticate users, Amazon Cognate user pools also support the OAuth 2.0 authorization framework for authenticating users. While each of these grant types is defined by the OAuth 2.0 RFC document, certain details about the endpoints are open-ended.
What is query string authentication?
Query String Authentication. Query String Authentication is where the access credentials (consumer key and consumer secret) are sent with each HTTP request as URL query parameters.
eSignature workflows made easy
Sign, send for signature, and track documents in real-time with signNow.