Substantiate Signed Request For Free
Note: Integration described on this webpage may temporarily not be available.
0
Forms filled
0
Forms signed
0
Forms sent
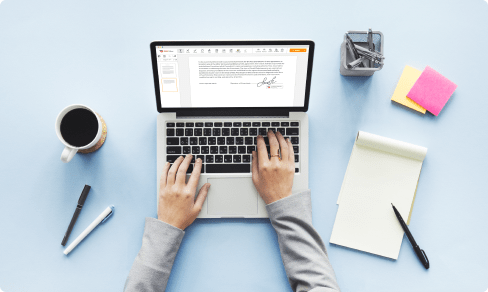
Upload your document to the PDF editor
Type anywhere or sign your form

Print, email, fax, or export

Try it right now! Edit pdf
Users trust to manage documents on pdfFiller platform
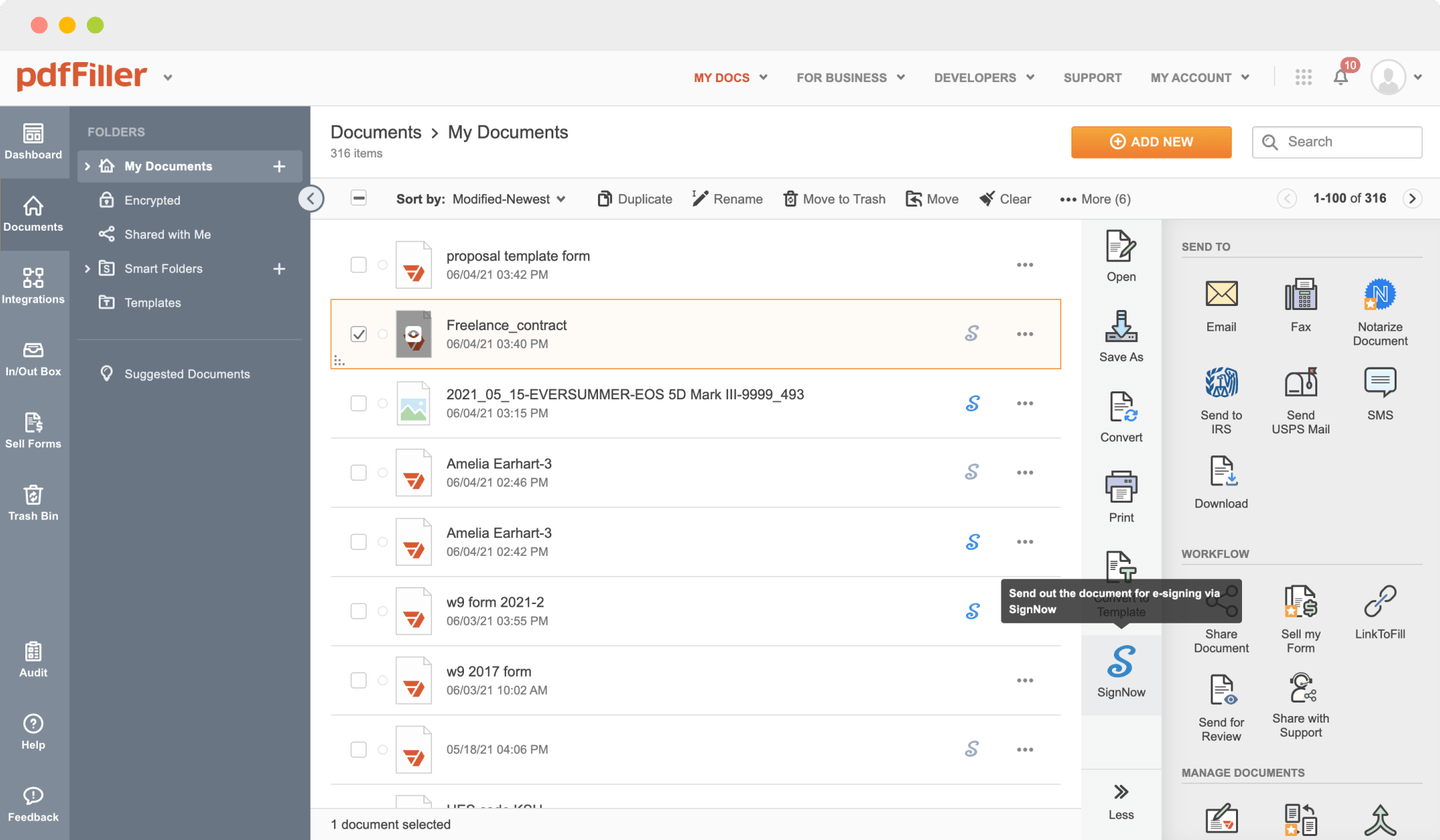
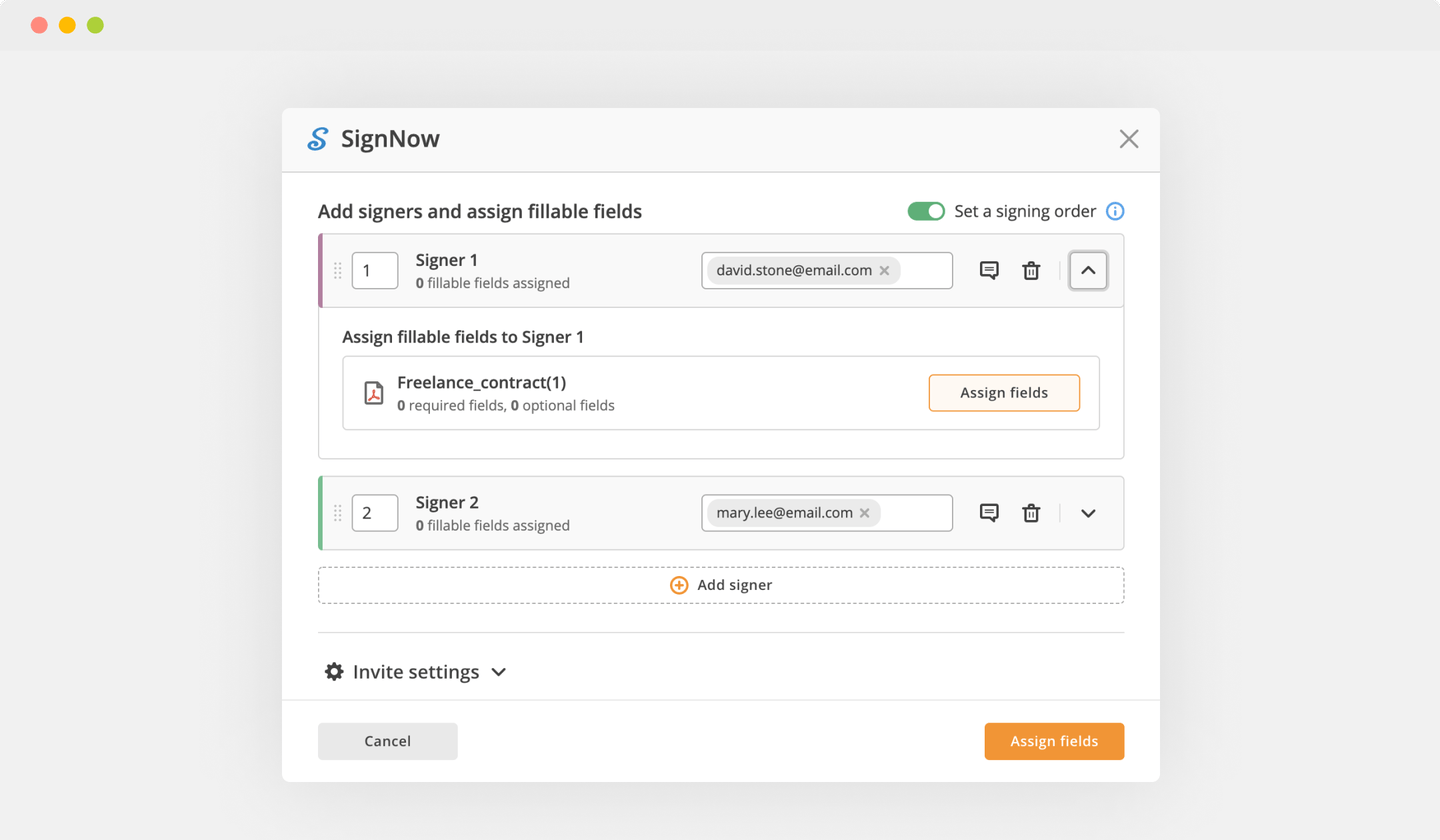
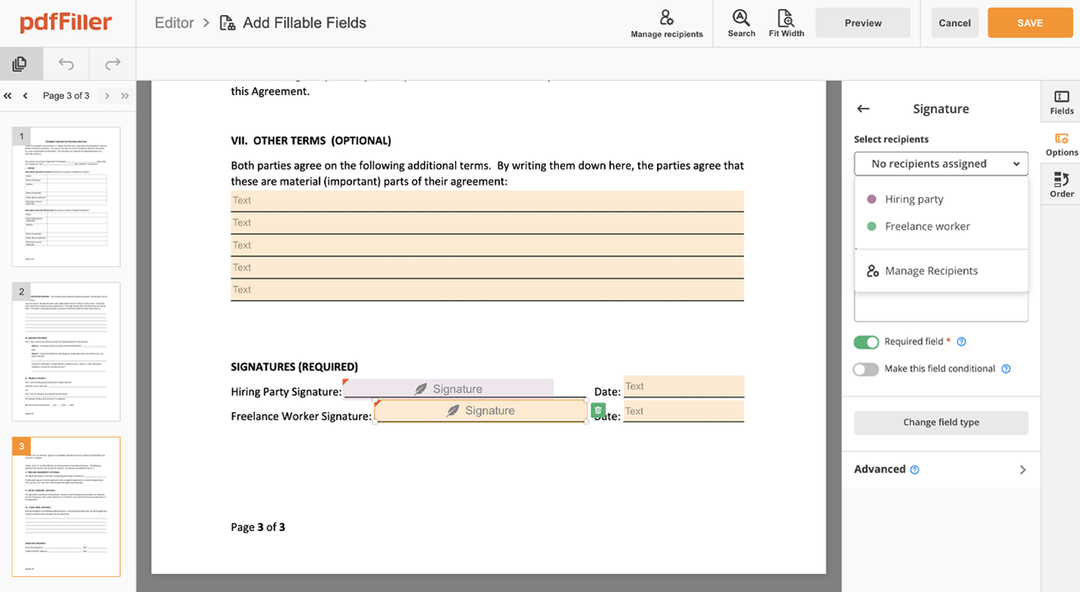
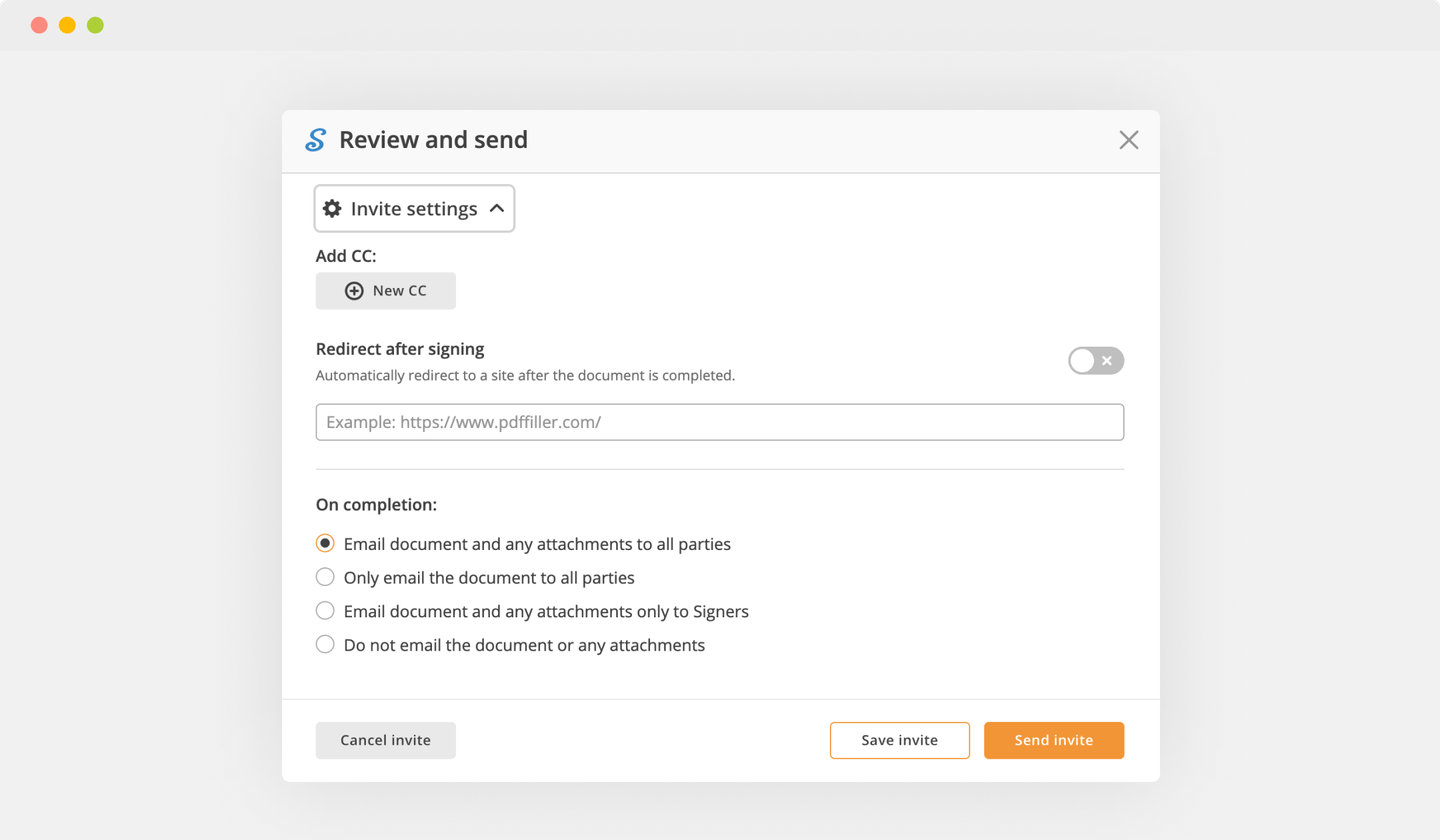
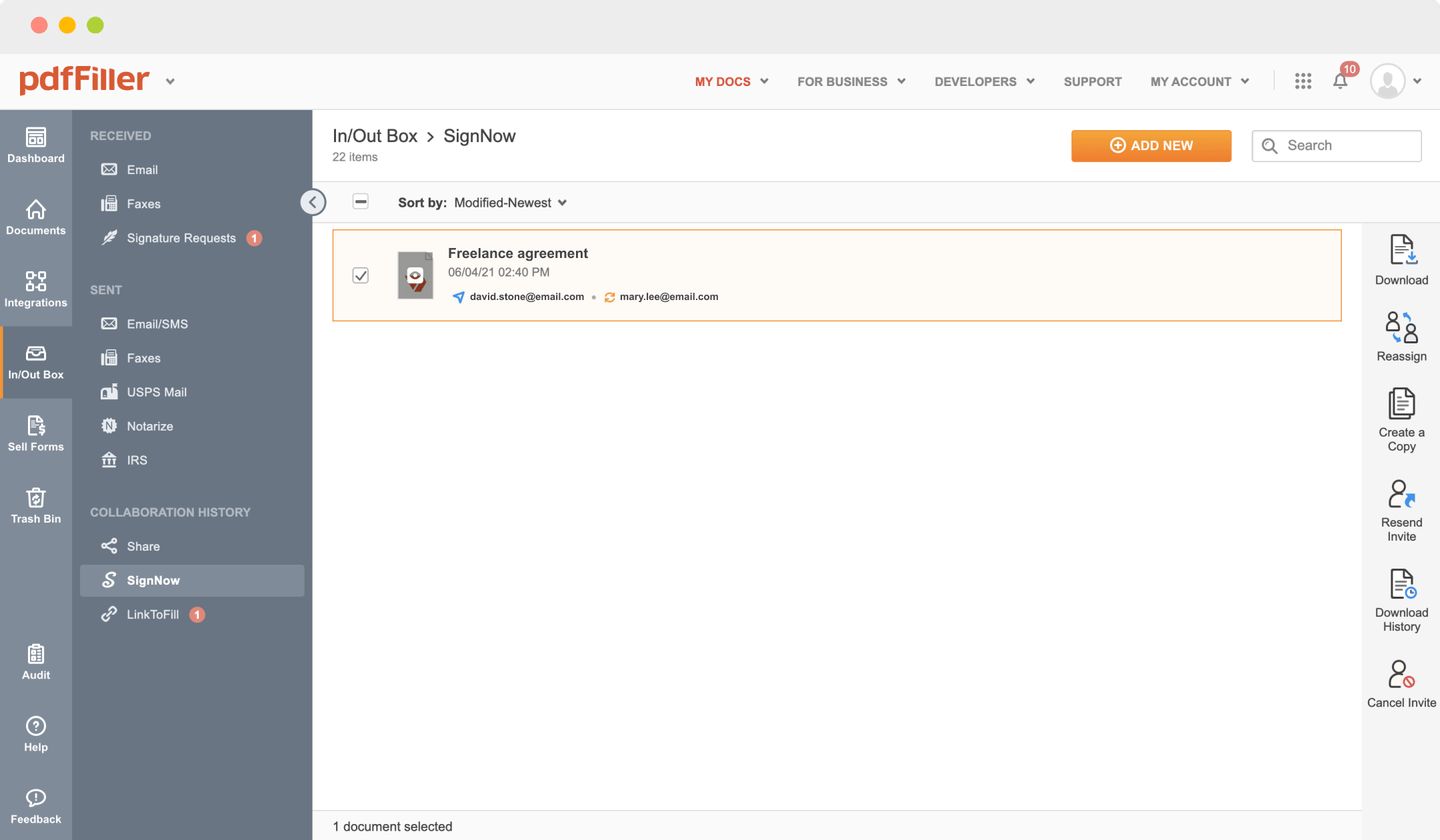
Send documents for eSignature with signNow
Create role-based eSignature workflows without leaving your pdfFiller account — no need to install additional software. Edit your PDF and collect legally-binding signatures anytime and anywhere with signNow’s fully-integrated eSignature solution.
All-in-one PDF software
A single pill for all your PDF headaches. Edit, fill out, eSign, and share – on any device.
pdfFiller scores top ratings in multiple categories on G2
How to Substantiate Signed Request
Stuck working with multiple applications to create and sign documents? We've got an all-in-one solution for you. Document management becomes simpler, fast and efficient with our platform. Create forms, contracts, make document templates, integrate cloud services and other features within your browser. Plus, the opportunity to Substantiate Signed Request and add major features like signing orders, reminders, attachment and payment requests, easier than ever. Get an advantage over those using any other free or paid programs.
How-to Guide
How to edit a PDF document using the pdfFiller editor:
01
Drag and drop your document using pdfFiller`s uploader
02
Select the Substantiate Signed Request feature in the editor's menu
03
Make the necessary edits to the document
04
Push “Done" button at the top right corner
05
Rename the form if it's required
06
Print, email or save the template to your desktop
What our customers say about pdfFiller
See for yourself by reading reviews on the most popular resources:
Montiqua
2015-04-15
I am enjoying the service. It is user friendly from a design point of view. I don't have feedback from the recipient experience however I will rate that component once I receive the feedback.

Jennifer M
2019-01-07
PDF filler has worked for our business through out the year and would highly recommend it. We mostly use it for fax purposes, but for us that alone is worth what we pay per year.


Get a powerful PDF editor for your Mac or Windows PC
Install the desktop app to quickly edit PDFs, create fillable forms, and securely store your documents in the cloud.

Edit and manage PDFs from anywhere using your iOS or Android device
Install our mobile app and edit PDFs using an award-winning toolkit wherever you go.

Get a PDF editor in your Google Chrome browser
Install the pdfFiller extension for Google Chrome to fill out and edit PDFs straight from search results.
List of extra features
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is request signing?
Request signature is the API request parameter api_sig which is added to every request to verify request user's authenticity on behalf of which the request is made. The request used to demonstrate request signing is a POST to https://infogr.am/service/v1/infographics.
What is http signature?
The HTTP Signatures specification is intended to provide a standard way for clients to add origin authentication and message integrity to HTTP-based messages. The HTTP Signature Nonce specification describes a way to use the HTTP Signatures protocol over an unsecured channel like HTTP.
What is request signature in Amazon API?
The input includes the text of your request and your secret access key. The hash function returns a hash value that you include in the request as your signature. The signature is part of the Authorization header of your request. Amazon API Gateway supports authentication using AWS Signature Version 4.
How do I make an AWS signature?
Use the canonical request and additional metadata to create a string for signing. Derive a signing key from your AWS secret access key. Then use the signing key, and the string from the previous step, to create a signature. Add the resulting signature to the HTTP request in a header or as a query string parameter.
What is SigV2?
In the early days of AWS we used a signing model that is known as Signature Version 2, or SigV2 for short. The newer signing method uses a separate, specialized signing key that is derived from the long-term AWS access key. The key is specific to the service, region, and date.
How do you sign a request?
To sign a request, you first calculate a hash (digest) of the request. Then you use the hash value, some other information from the request, and your secret access key to calculate another hash known as the signature.
How do you sign a document?
All you have to do is open your document, click “Tools," then click "Fill & Sign." Click the “Sign" button in the toolbar and you'll be prompted to type, draw or use an image of your signature.
What is signature version?
Signature Version V2 helps to maintain the integrity of the full APK. It is the whole-file signature scheme which helps to increase the speed of verification and provides the guaranteed integrity by detecting changes at the secured part of the APK.
What is query string authentication?
Query String Authentication. Query String Authentication is where the access credentials (consumer key and consumer secret) are sent with each HTTP request as URL query parameters.
What is canonical request?
A canonical request is a string that represents a specific HTTP request to Cloud Storage. You use a canonical request along with a cryptographic key, such as an RSA key, to create a signature that is then included in the actual request as authentication.
What is IAM role AWS?
An IAM role is an IAM entity that defines a set of permissions for making AWS service requests. IAM roles are not associated with a specific user or group. Instead, trusted entities assume roles, such as IAM users, applications, or AWS services such as EC2.
What does IAM mean?
An acronym for Identity and Access Management, IAM refers to a framework of policies and technologies for ensuring that the proper people in an enterprise have the appropriate access to technology resources. Also called identity management (IDM), IAM systems fall under the overarching umbrella of IT security.
eSignature workflows made easy
Sign, send for signature, and track documents in real-time with signNow.